Rug pulls are the defining scam of the DeFi era. Unlike hacks or exploits that require technical sophistication, rug pulls are engineered through social manipulation: a professional operation creates a token, builds hype through paid influencers and Telegram groups, attracts liquidity from retail investors, and then exits — draining the pool and leaving holders with worthless tokens. The entire process can take days to weeks. The financial damage to investors is typically 100% of their position.
The scale of the problem is significant. Research suggests that the vast majority of new DeFi pools on high-activity chains never survive their first month. On PancakeSwap alone, 95% of pools end in rug pulls. The challenge for investors is that every rug pull looks legitimate at launch — the social engineering is professional, the messaging is compelling, and the early price action is designed to build confidence before the exit.
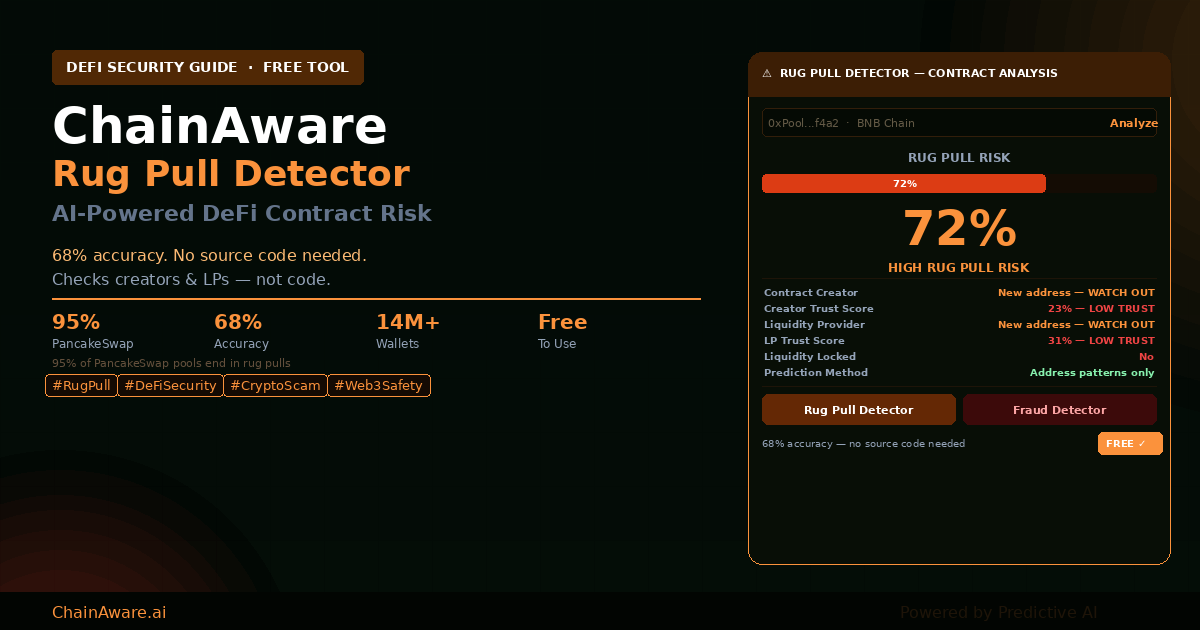
ChainAware’s Predictive Rug Pull Detector takes a different approach to identifying these risks: instead of analyzing smart contract source code (which requires technical expertise and can be obfuscated), it analyzes the behavioral Trust Scores of the people behind the contract — the creator and the liquidity providers. Good contracts are built by trusted actors. Bad contracts are typically built by new, anonymous, or low-trust addresses. This guide explains everything you need to know.
What Is a Rug Pull in Web3?
A rug pull is a type of exit scam specific to DeFi. The term comes from the expression “pulling the rug out” — the moment when the people behind a project withdraw all liquidity or drain the contract, leaving investors holding tokens with no backing and no exit.
Rug pulls typically follow one of two structural patterns. In a liquidity rug, the project team adds liquidity to a decentralized exchange pool to create a tradeable market for their token, attracts retail investment, and then removes all liquidity at once — crashing the token price to zero and leaving buyers unable to sell. In a backdoor rug, the smart contract itself contains a hidden function (often an unlimited mint, a privileged withdrawal, or a trading restriction for non-insiders) that allows the developers to drain funds or trap holders, regardless of the liquidity status.
What distinguishes rug pulls from other types of crypto fraud is the degree of premeditation and social engineering involved. A rug pull is not a hack or an accidental exploit — it is a deliberate plan executed by a team that builds the entire project for the purpose of the exit. According to Chainalysis’s research on crypto scam revenue, rug pulls and exit scams consistently rank among the highest-revenue fraud categories in the crypto ecosystem, with losses running into hundreds of millions annually.
Free Contract Risk Check
Check Any Pool or Contract Before You Invest
The ChainAware Rug Pull Detector analyzes the creator and liquidity providers of any smart contract using predictive AI — no source code required. Free. Real-time. Run your check before you commit capital.
How Rug Pulls Are Engineered: The Professional Scam Playbook
Rug pulling is not a cottage industry of opportunistic scammers. It is a professional operation with defined roles, repeatable playbooks, and increasingly sophisticated social engineering techniques. Understanding how rug pulls are constructed is essential to understanding why they’re so difficult to detect — and why behavioral analysis of the people behind the contract is more reliable than analysis of the contract itself.
Phase 1: Creating the Narrative
Every rug pull starts with a compelling story. The token solves a real problem, taps into a hot trend (AI, real-world assets, gaming, memecoins), and is positioned to be the “next big thing.” The narrative is designed to create urgency and FOMO. The whitepaper (if one exists) is polished and professional. The team may be anonymous but presents credible-seeming credentials.
Phase 2: Building the Hype Machine
Once the narrative is established, the hype machine activates. Paid KOLs (Key Opinion Leaders) on Twitter/X and YouTube post enthusiastic reviews. Telegram and Discord groups are seeded with thousands of members — many of them paid shills who post constantly about price targets and “100x potential.” The volume of positive messaging creates the illusion of organic community excitement. New investors see thousands of people talking about the project and interpret it as social proof.
The KOL problem in crypto is well-documented. As explored in our analysis of why influencer marketing isn’t working in Web3, many crypto KOLs promote projects for undisclosed fees without any due diligence — making them unwitting (or complicit) participants in the rug pull machinery.
Phase 3: The Price Pump
With hype established, the token price is pumped — often through coordinated buying among insiders, wash trading, and genuine retail FOMO from the social engineering in Phase 2. Early investors see rapid price appreciation, which creates additional urgency for latecomers. The pump generates screenshots of gains that are shared across social channels, amplifying the hype further.
This phase often overlaps with the pump-and-dump mechanics described in our dedicated guide — though in a rug pull, the exit mechanism is the liquidity drain rather than insiders selling their holdings.
Phase 4: The Exit
At peak hype and peak price, the rug pull executes. Liquidity is removed in a single transaction, or a backdoor function is triggered, or the team simply abandons the project and stops maintaining the contract. The token price collapses to near-zero within minutes. Holders are left with tokens they cannot sell, or can only sell at a 95-99% loss. The team moves the extracted funds through mixers or cross-chain bridges and prepares to launch the next project.
Why This Pattern Repeats
The rug pull cycle repeats because it is profitable and the barrier to entry is low. A new token can be launched in hours. A professional rug pull operation can run multiple projects simultaneously. The social engineering skills compound over time — each project is more convincing than the last. According to Immunefi’s annual Web3 security report, exit scams and rug pulls account for a significant and growing share of total crypto losses each year.
The Scale of the Problem: 95% of Pools
The most striking data point in DeFi security is this: approximately 95% of pools launched on PancakeSwap end in rug pulls. This is not a marginal problem affecting only careless investors — it is the dominant outcome for new DeFi pools on one of the world’s largest decentralized exchanges.
The implication is sobering: if you invest in a new PancakeSwap pool without any due diligence, your base rate expectation should be that it will rug pull. The 5% of legitimate projects are the exception, not the norm. Any tool that can identify even a portion of the 95% before the exit represents enormous value for investors.
This is precisely the problem the ChainAware Rug Pull Detector is designed to address. It does not claim to catch every rug pull — its 68% accuracy is honest about the limits of behavioral analysis without source code inspection. But identifying 68 out of every 100 rug pulls before they happen, from a free tool that takes seconds to use, represents a meaningful improvement over investing blind.
95% of New Pools Rug Pull
Don’t Invest Without Checking the Creator First
The Rug Pull Detector checks the Trust Score of the contract creator and liquidity providers — the behavioral signals that separate legitimate builders from rug pull operators. Free. Takes 10 seconds.
How the Rug Pull Detector Works
The ChainAware Rug Pull Detector is built on a core insight: a good contract can only be created by a trusted creator with trusted liquidity providers. Conversely, a bad contract will almost always have either a low-trust creator, low-trust liquidity providers, or both. By analyzing the behavioral Trust Scores of the addresses behind a contract rather than the contract’s source code, the detector identifies rug pull risk from the human pattern — not the technical one.
Step 1: Identify the Contract Creator
When you submit a contract address to the Rug Pull Detector, the first step is identifying the creator of that contract — the wallet address that deployed it. The detector runs this creator address through the ChainAware Fraud Detector to generate a Trust Score (1 minus the Fraud Score). A creator with a high Trust Score has a long, legitimate transaction history with behavioral patterns consistent with genuine builders. A creator with a low Trust Score, or a new address with minimal history, is a significant red flag.
Step 2: Trace Through Contract Creators
If the contract was deployed by another contract rather than a direct wallet address, the Rug Pull Detector traces through the chain of contracts until it reaches an underlying wallet address. Rug pull operators sometimes try to obscure their identity by routing deployment through intermediate contracts — this tracing step ensures the detector always reaches the human actor behind the contract.
Step 3: Analyze Liquidity Providers
After assessing the creator, the detector analyzes the liquidity providers (LPs) — the addresses that have added liquidity to the pool. Liquidity providers are critically important in rug pull detection because the exit mechanism in a liquidity rug pull is the LP removing their position. An LP with a low Trust Score or a new address adding significant liquidity is a strong indicator that the liquidity is “hot” — positioned for a quick exit rather than genuine market making.
Step 4: Generate the Rug Pull Risk Score
Based on the combined Trust Scores of the creator and liquidity providers, the detector generates an overall Rug Pull Risk probability. Key signals that elevate the risk score include: a new address as contract creator (new addresses have no behavioral history to establish trust); a new address adding liquidity (new LP addresses are a classic rug pull setup); low Trust Scores on creator or LPs (behavioral patterns inconsistent with legitimate actors); and lack of transparency — addresses that appear to be deliberately obscuring their history.
Conversely, risk scores are lowered when the creator has a long, clean on-chain history; liquidity providers have established Trust Scores; and the addresses are transparent — not routing through mixers or obfuscation layers.
Relationship to the Fraud Detector
The Rug Pull Detector and the Fraud Detector are complementary tools addressing different types of addresses:
The Fraud Detector analyzes regular wallet addresses (externally owned accounts) and predicts the probability that the address will commit fraud in the future. It works by identifying behavioral interaction patterns in the wallet’s transaction history that are characteristic of fraudulent activity.
The Rug Pull Detector analyzes smart contract addresses — specifically pools and protocol contracts — and predicts the probability of a rug pull. It does this by applying the Fraud Detector’s behavioral analysis to the human addresses behind the contract: the creator and the liquidity providers.
In other words: the Rug Pull Detector uses the Fraud Detector as its engine, but applies it to the people behind a contract rather than to any individual wallet. The relationship is: wallet risk = Fraud Detector; contract risk = Rug Pull Detector (which uses Fraud Detector internally).
For the full decision guide on which tool to use: checking a wallet address before a payment → Fraud Detector. Checking a contract or pool before investing → Rug Pull Detector. Full behavioral audit of a wallet → Wallet Auditor.
Accuracy: 68% Without Source Code
The current prediction accuracy of the ChainAware Rug Pull Detector is 68%. This means the algorithm correctly identifies 68 out of every 100 rug pulls based solely on address behavioral analysis — without reading or analyzing smart contract source code.
This number deserves context. 68% accuracy from behavioral analysis alone is a meaningful achievement for several reasons. First, smart contract source code can be obfuscated, copied from legitimate projects, or written to appear safe while containing hidden exploits — making source code analysis unreliable against sophisticated rug pull operators. Second, address behavioral patterns are much harder to fake: building a wallet with a legitimate-looking multi-year transaction history requires genuine time and on-chain activity. Third, the 68% figure comes from pure behavioral signal — no code inspection, no team identity verification, no social media analysis.
The honest implication is that the Rug Pull Detector is best used as a fast pre-screening tool. A high rug pull risk score is a strong signal to pause and investigate further. A low risk score is reassuring but not a guarantee — the remaining 32% of rug pulls that the tool misses are typically executed by more sophisticated operators who invest in building legitimate-looking creator histories before the exit.
According to Elliptic’s DeFi risk analysis, the most sophisticated rug pull operations specifically invest in establishing credible on-chain histories before deploying scam contracts — which is precisely the category the 32% miss rate captures. For high-value investments, combining the Rug Pull Detector with source code analysis from specialized audit tools provides the most complete risk picture.
68% Accuracy — No Code Reading Required
Rug Pull Detector: Fast Pre-Screening for Any DeFi Contract
In 10 seconds, get a behavioral risk score on the creator and LPs behind any pool or contract. Predictive AI. No technical expertise needed. Free. Use it before every new DeFi investment.
Key Red Flags the Detector Identifies
New contract creator address. If the wallet that deployed the contract was created recently with few prior transactions, there is no behavioral history to assess. Legitimate builders typically deploy from wallets with established on-chain histories. A fresh deployment address is one of the strongest rug pull signals, because rug pull operators routinely create new wallets for each project to avoid connecting their new scam to their previous exit history.
Low Trust Score on the creator. A creator address with an established but low Trust Score is arguably even more dangerous than a new address — it means the wallet has a behavioral history, and that history includes patterns associated with fraudulent activity. This is the profile of a repeat rug pull operator who has built some on-chain history but whose interaction patterns still betray their intent.
New liquidity provider addresses. Liquidity added by freshly-created addresses is a classic rug pull setup. New LP addresses have no behavioral track record, and their liquidity is statistically likely to be “hot” — intended for rapid removal rather than genuine market making. The Rug Pull Detector flags new LP addresses prominently because the liquidity removal is the mechanism of the exit.
Low Trust Score on liquidity providers. LPs with established but low Trust Scores suggest that the liquidity is being provided by entities with fraudulent behavioral histories — potentially the same rug pull ring operating under different addresses.
Hidden or obfuscated creator chain. When the contract was deployed through a chain of intermediate contracts that obscures the ultimate creator, this is itself a red flag. Legitimate builders have no reason to obscure the chain of contract creation. The Rug Pull Detector notes when it has had to trace through multiple layers to find the underlying creator address.
How to Use the Rug Pull Detector
Navigate to chainaware.ai/rug-pull-detector. Connect your wallet for free access. Enter the contract address of the pool or token you want to assess and select the appropriate blockchain network.
The detector returns a Rug Pull Risk score alongside the individual Trust Scores of the contract creator and key liquidity providers. Review the scores in context: a single low-trust LP among several high-trust LPs is less alarming than a low-trust creator — the creator is the most important signal, followed by the largest liquidity providers.
Use the result as a pre-screening filter. A high rug pull risk score (above 0.7) should prompt you to either avoid the investment entirely or conduct significantly deeper due diligence before committing. A low risk score (below 0.3) is encouraging but not a guarantee — remember the 32% miss rate for sophisticated operators.
For any wallet address in the results that you want to investigate further, use the Wallet Auditor for a full behavioral profile including Trust Score, AML status, experience level, risk willingness, and Wallet Rank.
Why Address Analysis vs Source Code Analysis?
Most rug pull detection tools on the market analyze smart contract source code — looking for specific dangerous patterns like unlimited mint functions, trading restriction mechanisms, or privileged withdrawal functions. This approach has real value but significant limitations.
Source code analysis requires the source code to be available and verified. Many rug pull contracts are not verified on-chain, making code analysis impossible. Even when verified, professional rug pull operators copy audited, legitimate contract code as a base — hiding exploits in subtle modifications that automated tools miss. Code analysis also requires technical expertise to interpret meaningfully; most retail investors cannot read Solidity.
Address behavioral analysis sidesteps all of these limitations. The behavioral history of a wallet cannot be faked in real-time — it is the accumulated record of every transaction that address has ever made. A rug pull operator cannot instantly create the on-chain profile of a legitimate builder. This is the core advantage of ChainAware’s approach: the signal is in the people, not the code.
The two approaches are complementary. For maximum security on high-value investments, combine the Rug Pull Detector’s behavioral screening with source code analysis from a specialized audit service. For rapid pre-screening of new pools before allocating capital, the Rug Pull Detector’s free, instant, no-technical-expertise-required analysis provides actionable signal that most investors currently have no access to.
Where It Fits in the ChainAware Ecosystem
The Rug Pull Detector sits at the intersection of ChainAware’s fraud intelligence and its broader Predictive Data Layer. It uses the same underlying Trust Score engine as the Fraud Detector, applied specifically to the contract context. The 14M+ wallet behavioral profiles in ChainAware’s Predictive Data Layer power the instant Trust Score lookups that the Rug Pull Detector relies on for creator and LP assessment.
For token-level due diligence — assessing the quality of a token’s existing holder base rather than its pool creator — the Token Rank provides a complementary signal: a token whose holders have high average Wallet Ranks is less likely to be a rug pull operation than one dominated by low-quality wallets.
For Dapp teams who want to integrate rug pull risk screening into their own products, the full Predictive Data Layer is accessible via the Prediction MCP — enabling AI agents to query Trust Scores, fraud probabilities, and behavioral profiles programmatically in real time.
Real-World Use Cases
1. New Pool Investor: Pre-Investment Screening
You’ve seen a new token trending on Telegram and Twitter/X. Before committing any capital, run the contract address through the Rug Pull Detector. If the creator is a new address or has a low Trust Score, the hype is almost certainly manufactured. Close the Telegram tab and move on. If the creator and LPs have high Trust Scores and established histories, you have one positive signal among several you should gather before investing.
2. Liquidity Provider: Before Adding to a New Pool
Providing liquidity in a pool where one of the other LPs has a low Trust Score exposes you to coordinated liquidity removal risk — where insiders drain the pool before you can react. Checking the Trust Scores of existing LPs before adding your own liquidity takes seconds and can prevent significant losses.
3. Token Project Team: Establishing Legitimacy
Legitimate project teams can use the Rug Pull Detector proactively — sharing their high Trust Score results publicly as evidence that the contract creator and LPs have established, legitimate behavioral histories. In a market where 95% of pools rug pull, a verifiable low rug pull risk score is a genuine competitive differentiator for attracting cautious investors.
4. DeFi Aggregator or Launchpad: Automated Screening
Platforms that list new tokens or pools can integrate the Rug Pull Detector’s behavioral screening as an automated gate — surfacing risk scores alongside pool listings to help users make more informed decisions. For automated API integration, see the Prediction MCP developer guide.
5. Portfolio Manager: Ongoing Monitoring
The behavioral profiles of contract creators and LPs can change over time as they interact with more protocols. Periodic re-screening of pools you’re already invested in — particularly if you notice unusual price or volume behavior — can provide early warning of elevated rug pull risk before the exit executes.
ChainAware.ai — DeFi Fraud Intelligence
Check the Contract. Check the Creator. Check the LPs.
Rug Pull Detector for smart contracts and pools. Fraud Detector for wallet addresses. Both free. Both predictive. Both real-time. Don’t invest without checking first.
Frequently Asked Questions
What is the difference between the Rug Pull Detector and the Fraud Detector?
The Fraud Detector analyzes regular wallet addresses and predicts the probability of fraud. The Rug Pull Detector analyzes smart contract addresses (pools, token contracts) and predicts the probability of a rug pull — it does this by applying the Fraud Detector’s Trust Score analysis to the contract’s creator and liquidity providers.
Does the Rug Pull Detector read smart contract source code?
No. The Rug Pull Detector analyzes address behavioral patterns only — the Trust Scores of the contract creator and liquidity providers. It does not inspect, read, or analyze smart contract source code. This makes it accessible to non-technical users and effective even when source code is not publicly verified.
What does 68% accuracy mean in practice?
It means the algorithm correctly identifies 68 out of every 100 rug pulls based on behavioral signals alone. The 32% it misses are typically from more sophisticated operators who invest in building legitimate-looking creator histories. Use the detector as a fast pre-screening tool: a high risk score is a strong red flag; a low risk score is encouraging but not a guarantee.
Why is a new creator address a red flag?
Because rug pull operators routinely create fresh wallets for each project to disconnect their new scam from their previous exit history. A new address has no behavioral history, making Trust Score assessment impossible — and statistically, new deployment addresses are strongly associated with rug pull activity versus legitimate builders who deploy from established wallets.
Is the Rug Pull Detector free?
Yes — completely free. Connect your wallet for access and run as many checks as you need. No subscription, no credits, no fee per lookup.
Can I use this on any blockchain?
The Rug Pull Detector supports the same networks as the Fraud Detector: Ethereum, Binance Smart Chain, Base, Polygon, Haqq, Solana, TON, and Tron.
What should I do if a pool shows high rug pull risk?
Treat it as a strong signal to avoid the investment or conduct significantly deeper due diligence before committing capital. Check the individual wallet addresses flagged using the Wallet Auditor for full behavioral profiles. Consider combining with source code analysis from a specialized audit service for high-value investments.