Crypto theft hit a new record in 2025. According to Chainalysis’s 2025 Crypto Crime Report, illicit activity involving crypto wallets — spanning phishing, rug pulls, smart contract exploits, private key theft, and social engineering — accounted for tens of billions in losses from individual users and protocols alike. The attack surface is expanding. The sophistication of threats is growing. And the defenses most crypto users rely on are falling behind.
The conventional security advice — use a hardware wallet, never share your seed phrase, check contract addresses carefully — remains valid. But it is no longer sufficient. These measures protect against threats you can see coming. They do nothing to protect you from the threats you cannot see: the counterparty whose wallet looks legitimate but whose behavioral history contains every pattern associated with fraud preparation; the liquidity pool whose contract passes a surface audit but whose creator wallet has already run two previous rug pulls.
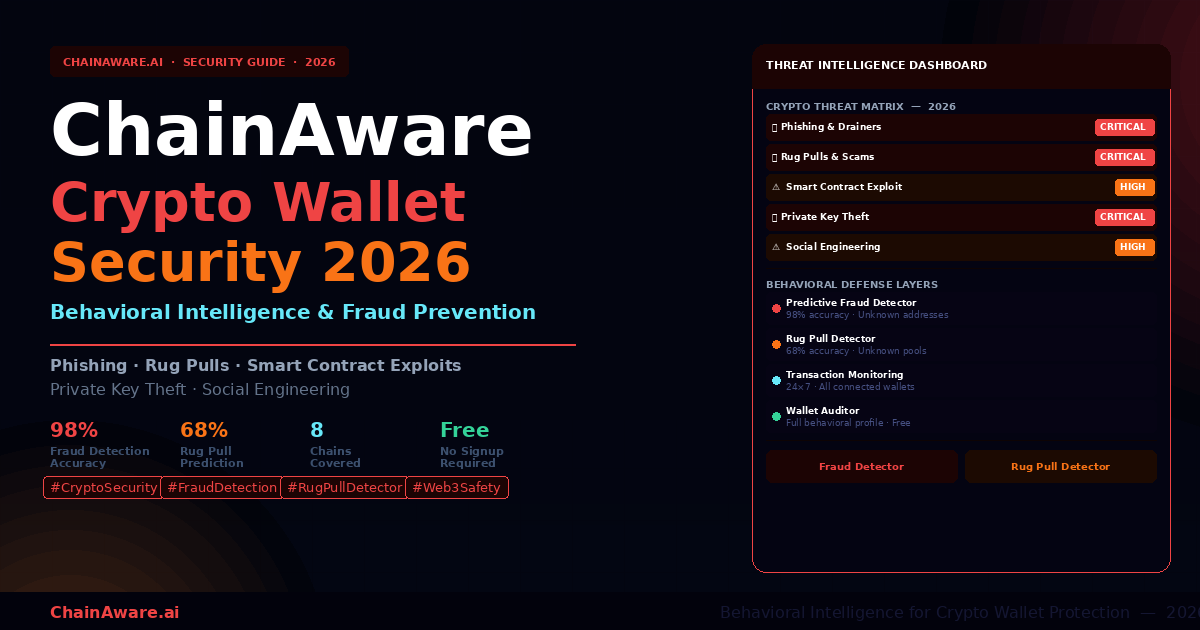
Behavioral intelligence is the security layer that closes these gaps. Rather than checking whether a counterparty’s funds are clean, behavioral AI predicts whether that counterparty is likely to commit fraud based on their on-chain behavioral history — with 98% accuracy, in real time, before you send a single satoshi.
This guide covers the full 2026 threat landscape: what each major attack vector looks like, how it has evolved, where traditional defenses succeed and where they fail, and how behavioral intelligence addresses the gaps that conventional security cannot close.
The 2026 Crypto Threat Landscape: Scale and Evolution
Three structural factors make crypto uniquely vulnerable. First, irreversibility: blockchain transactions cannot be reversed. Second, pseudonymity: most addresses are not linked to verified identities — the only record is on-chain behavioral history. Third, complexity and speed: DeFi moves faster than most users can evaluate safely. According to the US Federal Trade Commission, urgency is the most consistently reported feature of successful crypto scams.
Estimated annual crypto losses to fraud, theft & scams (Chainalysis 2025)
Fraud prediction accuracy of ChainAware’s Predictive Fraud Detector
Increase in AI-assisted phishing and social engineering attacks since 2023
Threat 1: Phishing, Wallet Drainers & Approval Attacks
Phishing & Wallet Drain Attacks
What it is: Deceptive attempts to trick users into connecting their wallet to a malicious site or signing a transaction that grants an attacker access to their funds.
2026 evolution: AI-generated phishing sites now replicate legitimate Dapps with pixel-perfect accuracy. Wallet drainer contracts are increasingly disguised as standard approval transactions.
How it works: A user receives a Discord message about an exclusive NFT mint. The link leads to a site identical to a known collection. Connecting the wallet triggers a setApprovalForAll transaction granting the attacker control over all assets. The drain completes in seconds.
Classic phishing uses homograph attacks — lookalike Unicode URLs invisible to the naked eye. Approval phishing tricks users into signing unlimited spending permissions. According to Elliptic’s DeFi risk research, approval phishing now accounts for the majority of high-value individual crypto theft. Airdrop drain attacks send worthless tokens whose interaction triggers drain contracts.
Threat 2: Rug Pulls and Exit Scams
Rug Pulls & Liquidity Exit Scams
What it is: A project team raises funds or liquidity, then abruptly withdraws all value and abandons the project.
2026 evolution: Modern rug pulls feature professional websites, audited-looking contracts, and active communities maintained for weeks before the exit.
How it works: A DeFi yield protocol launches with high APY. Liquidity accumulates over 2–4 weeks. The team wallet withdraws all liquidity in a single transaction, leaving depositors with unsellable tokens.
Variants: hard rug (instant total drain), soft rug (gradual team sell-off), slow abandonment, and honeypot contracts (buy but cannot sell). The most dangerous misconception is that a smart contract audit makes a protocol safe — audits check code, not intentions. The ChainAware Rug Pull Detector checks the behavioral history of creator wallets, not source code.
Free — Check Before You Transact
Predictive Fraud Detector: Know If an Address Is Safe Before Sending Funds
Before sending crypto to an unknown address, run it through the Predictive Fraud Detector. AI behavioral analysis predicts fraud probability with 98% accuracy. Free, instant, covers 8 chains.
Threat 3: Smart Contract Exploits
Smart Contract Exploits & DeFi Hacks
What it is: Attacks exploiting vulnerabilities in smart contract code to extract funds from protocols, affecting all users.
2026 evolution: Flash loan attacks are highly automated. Cross-chain bridge vulnerabilities remain one of the largest attack surfaces.
How it works: An attacker takes a $50M flash loan, manipulates a lending protocol’s price oracle, borrows against inflated collateral, extracts $30M in real assets, and repays the loan — all in a single block.
Major categories: reentrancy attacks, oracle manipulation, access control flaws, and cross-chain bridge exploits (Ronin $625M, Wormhole $320M). See our AI-Powered Blockchain Analysis guide.
Threat 4: Private Key and Seed Phrase Theft
Private Key Theft & Seed Phrase Compromise
What it is: Any attack resulting in permanent, irrevocable control over a wallet’s assets.
2026 evolution: Keyloggers, clipboard hijackers, browser extension compromises, and supply chain attacks have all increased significantly.
How it works: A developer downloads a compromised npm package that silently scans for wallet files and .env files containing private keys, then exfiltrates them to an attacker-controlled server.
The four paths: malware/info-stealers (RedLine, Raccoon, Vidar), clipboard hijacking, seed phrase phishing (fake recovery sites), and supply chain attacks. See our Predictive AI for Crypto KYC & AML guide.
- Hardware wallet (Ledger, Trezor, Coldcard) for any significant holdings
- Seed phrase offline only — paper or metal, never digital or photographed
- Dedicated device for crypto transactions
- Transaction simulation to preview what each transaction does before signing
- Never enter a seed phrase anywhere except your hardware wallet’s physical interface
- Audit active token approvals regularly using Revoke.cash
- Multi-signature wallets for organizational or high-value holdings
Threat 5: Social Engineering and Impersonation
Social Engineering, Pig Butchering & Impersonation
What it is: Manipulation attacks exploiting human psychology — trust, greed, urgency — rather than technical vulnerabilities.
2026 evolution: AI voice cloning and deepfakes have made impersonation dramatically more convincing. Pig butchering scams now operate at industrial scale via AI chatbots.
How it works: An investor builds rapport with a fake professional contact over weeks, then deposits significantly into a fraudulent high-yield platform, finding they cannot withdraw without paying escalating fees to the attacker.
Vectors: pig butchering (FBI reports this as the largest single category of crypto fraud losses), fake team impersonation, support scam DMs, and undisclosed KOL paid promotion. As documented in our influencer marketing in crypto analysis, on-chain behavioral history is the most reliable legitimacy signal.
“Social engineering exploits the one vulnerability that hardware wallets and audits cannot address: human judgment under manufactured urgency and misplaced trust. The defense is systematic counterparty verification — not faster decision-making.”
Traditional Defenses: What They Cover and Where They Fail
The critical gap is counterparty behavioral risk — every traditional measure protects your own wallet but tells you nothing about the other party. See our Transaction Monitoring vs AML guide.
The Behavioral Intelligence Layer
Behavioral intelligence is built on a foundational insight: on-chain behavioral history is the most reliable predictor of future fraudulent behavior. Fraud patterns — mixing protocol usage, sybil cluster coordination, anomalous transaction timing — are detectable by AI models trained on millions of confirmed fraud cases across 8 blockchains. Fraud is frequently committed with clean funds — professional operators fund attack wallets through legitimate channels to pass AML checks. Behavioral patterns reveal intent where fund origin cannot. See our Forensic vs AI-Powered Blockchain Analysis guide.
On-Chain Transaction History
+ Protocol Interaction Patterns
+ Fund Movement Timing
+ Counterparty Network Analysis
+ Sybil/Coordination Signals
+ Mixing Protocol Usage
────────────────────────────────
→ Fraud Probability Score (0–100%)
→ Prediction Accuracy: 98%
Fraud Detector: Check Unknown Addresses Before Transacting
The ChainAware Predictive Fraud Detector evaluates any wallet address across seven behavioral dimensions: transaction patterns, counterparty network mapping, protocol interaction history, mixing protocol detection, sybil cluster analysis, fund movement patterns, and AML status. Output is a Trust Score — 95%+ is clean, below 50% warrants caution, below 30% is a strong warning. Use before sending funds to any new counterparty, interacting with a new contract deployer, or joining any new protocol. See the Fraud Detector complete guide.
Rug Pull Detector: Screen Unknown Pools and Contracts
The ChainAware Predictive Rug Pull Detector checks the behavioral history of the humans behind a contract — creator wallet history, LP provider profiles, token distribution patterns, and cross-protocol behavioral signatures. 68% accuracy catches rug pull risk that code audits entirely miss. Use when: launched within 90 days, APY above 50%, anonymous team, heavy KOL promotion, or no reputable audit. See the Rug Pull Detector complete guide.
Free — Check Before You Deposit
Predictive Rug Pull Detector: Know If a Pool Is Safe Before Depositing
Before providing liquidity or staking tokens in any DeFi pool — run the contract through the Rug Pull Detector. AI behavioral analysis of creator and LP wallets predicts rug pull probability. Free, instant.
The Complete 2026 Wallet Security Workflow
Layer 1: Key and Device Security
- Hardware wallet for all significant holdings
- Seed phrase offline only — never photographed, never in cloud storage
- Dedicated device for crypto transactions where possible
- Active token approval management — audit and revoke unused approvals monthly
- Multi-signature wallet for organizational funds or holdings above $50,000
Layer 2: Transaction Verification Before Signing
- Verify site URLs character-by-character before connecting wallet
- Use transaction simulation to preview exactly what each transaction will do
- Never sign setApprovalForAll without independently verifying the requesting protocol
- Urgency is a social engineering signal — always pause for high-value transactions
Layer 3: Counterparty Behavioral Intelligence
- Run the Fraud Detector on any address you’re sending significant funds to for the first time
- Run the Rug Pull Detector on any pool or contract you haven’t previously vetted
- Check the Wallet Auditor profile of significant counterparties — KOLs, advisors, partners
- Consider the Transaction Monitoring Agent for ongoing protocol relationships
Layer 4: Social Engineering Defense
- Verify all urgent communications through official channels before acting
- No legitimate team will contact you unsolicited via DM with opportunities or alerts
- KOL endorsements are not security validation — check on-chain profiles independently
- If an opportunity requires immediate action, that urgency is itself a red flag
For Platforms: Protecting Users at the Protocol Level
The Transaction Monitoring Agent deploys via Google Tag Manager and continuously screens every connecting wallet 24×7. When a wallet’s Trust Score drops significantly, your team receives an immediate Telegram alert. The Credit Scoring Agent monitors borrower creditworthiness continuously for lending protocols. See the ChainAware complete product guide.
Frequently Asked Questions
What is the single most important thing I can do to secure my crypto wallet in 2026?
Use a hardware wallet for significant holdings and never store your seed phrase digitally. This addresses the most catastrophic failure mode — private key theft — which results in total, irrecoverable loss.
How is behavioral intelligence different from AML tools?
AML tools verify the origin of funds. Behavioral intelligence predicts future fraudulent behavior based on on-chain activity patterns. The critical difference: fraud is frequently committed with clean funds. A professional operator who funds their wallet legitimately passes any AML check — but their behavioral patterns reveal intent.
Can the Fraud Detector evaluate an address that sent funds TO me?
Yes — it works on any wallet address regardless of fund flow direction. Unexpected deposits can indicate taint attacks or drain airdrop setups. Do not interact with tokens from high-fraud-probability addresses without investigation.
Does checking an address reveal my identity to the address owner?
No. The query is entirely one-directional — reading publicly available on-chain data. The owner has no visibility into who checked their address and no on-chain transaction is generated.
What’s the difference between the Rug Pull Detector and a smart contract audit?
Audits check code quality and technical vulnerability. The Rug Pull Detector checks the behavioral history of the people controlling the contract. A technically perfect contract can still be used to rug investors — the Rug Pull Detector catches this risk that code audits miss entirely.
How accurate are the tools?
The Fraud Detector achieves 98% accuracy predicting fraudulent behavior before it occurs. The Rug Pull Detector achieves 68% accuracy. Both are risk signals to inform your decision — not binary verdicts replacing your own judgment.
What blockchains are covered?
The Fraud Detector covers Ethereum, BNB Chain, Base, Polygon, Solana, TON, Tron, and Haqq. The Rug Pull Detector covers Ethereum, BNB Chain, Base, and the major chains where new DeFi pool activity is concentrated.
Is a hardware wallet still necessary if I use behavioral intelligence tools?
Yes — they address completely different threat vectors. A hardware wallet protects your private keys. Behavioral intelligence evaluates counterparty risk. The complete security posture requires both layers.
ChainAware.ai — Behavioral Intelligence for Safer Crypto
Check Any Address or Pool Before You Commit Funds
Fraud Detector · Rug Pull Detector · Wallet Auditor — the complete stack for crypto users who want to screen counterparty risk with AI behavioral intelligence. Free tools, no account required, instant results.