Two statistics define the danger landscape for crypto investors in 2026. First: approximately 95% of new pools launched on PancakeSwap end in rug pulls. Second: a significant proportion of the remaining 5% that don’t immediately rug pull become something arguably more insidious — slow, professionally engineered pump-and-dump schemes that extract retail wealth over months or years before the final collapse.
These are not edge cases or amateur mistakes. Rug pulls and pump-and-dump schemes are the two primary mechanisms of a sophisticated, highly profitable fraud industry that specifically targets crypto newcomers and retail investors. They are built by professionals, executed with precision, and engineered to maximize wealth extraction while minimizing legal exposure. And they are directly responsible for the pattern that limits the growth of the entire crypto sector: enthusiasts enter with excitement, get scammed, and leave permanently.
This guide explains exactly how both scam types work, why they’re so effective, and what concrete tools you can use to protect yourself before you invest.
What Is a Rug Pull? The Fast Exit
A rug pull is a deliberate exit scam executed on a DeFi protocol. The team behind a project — typically anonymous — creates a token, builds artificial hype, attracts investor liquidity, and then exits suddenly by draining the pool. Investors are left holding tokens with no liquidity and no exit. The price drops to zero instantly. The loss is typically 100% of invested capital.
The term comes from the expression “pulling the rug out” — the floor disappears beneath investors without warning. Unlike a hack or technical exploit (which are accidental from the project team’s perspective), a rug pull is entirely intentional. The project was built for the exit. Every marketing effort, every community post, every price pump was infrastructure for the theft.
According to Chainalysis crypto crime research, rug pulls and exit scams consistently rank among the highest-revenue fraud categories in crypto — generating billions in annual losses for retail investors. The scale of the problem is why 95% of new DEX pools on high-activity chains like PancakeSwap never survive their first weeks.
Rug Pull Mechanics: Two Exit Methods
There are two primary technical mechanisms through which rug pulls execute the exit:
Method 1: Liquidity Drain
The most common form. The project team creates a token pair on a DEX (e.g., TOKEN/BNB or TOKEN/USDT) and adds initial liquidity — creating a tradeable market. Retail investors buy TOKEN, adding their BNB or USDT to the liquidity pool. When the team decides the exit timing is right, they remove their LP tokens (liquidity provider tokens), withdrawing all the pooled BNB/USDT. The token is now untradeable — there is no liquidity to sell into. The price drops to zero. Holders are left with worthless tokens and no recourse.
Method 2: Mint-and-Dump
In this variant, the smart contract contains a hidden or backdoor minting function that allows the team to create arbitrary new tokens at will. When the exit is triggered, the team mints an enormous quantity of new tokens and immediately sells them into the existing liquidity pool — crashing the price and draining the pool simultaneously. Holders see the price collapse in real time but by the time any individual responds, the exit is complete.
Both methods produce the same outcome for investors: total loss. The difference is that mint-and-dump attacks are harder to detect from the contract side (the minting function may be hidden or obfuscated), which is why behavioral analysis of the people behind the contract — rather than the contract code — is a more reliable detection method. See our complete Rug Pull Detector guide for how this works.
How Rug Pulls Are Engineered
Rug pulling is not opportunistic crime. It is a professional industry with standardized playbooks, economies of scale, and increasing sophistication year over year. Understanding the engineering behind it is essential to recognizing it before you’re inside the trade.
Step 1: Narrative creation. Every rug pull starts with a compelling story. The token solves a real problem, rides a hot trend (AI, RWA, gaming, memecoins), or promises enormous returns. The narrative is crafted to create FOMO: “10x guaranteed,” “100x potential,” “next Shiba Inu.” Whitepapers are written, websites are built, roadmaps are published. All of it is theatre.
Step 2: Hype machine activation. Paid KOLs post positive content. Telegram and Discord groups are seeded with thousands of members — many of them paid shills posting price targets and hype 24/7. The volume of positive signals creates the illusion of genuine community excitement. As analyzed in our guide to why influencer marketing isn’t working in Web3, many KOLs promote projects without any due diligence — making them instruments of the rug pull machinery.
Step 3: Price pump. Coordinated buying among insiders, wash trading, and genuine retail FOMO drive the price upward. Screenshots of gains circulate on social media, attracting more buyers. The rising price is itself the most powerful marketing tool — nothing creates FOMO like watching a number go up.
Step 4: The exit. At peak hype and peak price, the rug pulls. Liquidity is drained or tokens are minted and sold in a matter of minutes or seconds. The price collapses to zero. The team disappears. The Telegram group goes silent or is deleted. The website goes offline. And the operation prepares to repeat with a new token and a new identity.
95% of New Pools Rug Pull — Check Before You Invest
ChainAware Rug Pull Detector: Predict Pool Risk Before It Happens
Checks the Trust Scores of the contract creator and liquidity providers using predictive AI. 68% accuracy without reading source code. Free. Takes seconds. Run it before adding liquidity to any new pool.
What Is a Pump and Dump? The Long Rug Pull
If a rug pull is a smash-and-grab, a pump-and-dump scheme is a long con. The core mechanics are the same — insiders accumulate tokens early, manufacture artificial demand, sell into that demand, and exit — but the timeline stretches from days to months or years, and the infrastructure is dramatically more sophisticated.
In the crypto context, pump-and-dump schemes are what the 5% of DEX pools that don’t immediately rug pull often become. They get a CEX listing. They hire market makers. They build a real (or appearing-real) product. They maintain the narrative for long enough to attract ongoing waves of retail buyers who serve as exit liquidity for the insiders’ gradual position liquidation.
The defining characteristic of a pump-and-dump scheme is this: the price chart looks like slow, grinding decline punctuated by coordinated pumps. Every pump attracts new buyers. Those buyers become exit liquidity for insiders selling into the pump. The price recovers partially, enough to maintain hope, then grinds lower. Rinse, repeat, until there is nothing left to extract and the team walks away.
According to Bank for International Settlements research on crypto market surveillance, pump-and-dump manipulation is detectable in a significant proportion of smaller-cap crypto assets — and the manipulation typically runs for extended periods before the final collapse.
Pump and Dump Mechanics: Manufacturing Reality
A professional pump-and-dump operation in 2026 looks, from the outside, almost identical to a legitimate project. This is by design. Here is the full playbook:
Phase 1: Stealth accumulation. Insiders accumulate the token at very low prices — before any public marketing. This is the foundation of the scheme: insiders hold a large percentage of the supply at near-zero cost. Everything that follows is infrastructure for eventually selling these tokens to retail at a profit.
Phase 2: Narrative and marketing launch. The project launches with a sophisticated marketing operation: professional website, detailed whitepaper, active social media presence, YouTube explainers, blog content, and a constant stream of “development updates.” The project may actually build something — not because it will deliver value, but because a working product makes the story more credible and the exit runway longer.
Phase 3: CEX listing and market maker engagement. A CEX listing dramatically expands the potential buyer pool. Centralized exchange users bring fresh capital. Market makers are hired (or are insiders themselves) to maintain orderly-looking price action and manufactured trading volume. The price chart looks like a growing asset, not a manipulation in progress.
Phase 4: Continuous drip selling. Every week, insiders sell a portion of their holdings into the buying pressure generated by ongoing marketing. The selling is calibrated to not crash the price — just enough to extract value while maintaining enough price stability to keep new buyers entering. KOL campaigns, exchange listings, partnership announcements, and product releases are all timed to generate buying pressure that absorbs insider selling.
Phase 5: The final dump. When the insider position is largely liquidated, or when maintaining the narrative becomes too expensive, the final dump occurs — often coordinated with one last marketing push to attract maximum exit liquidity. The price collapses. The team declares the project is “pivoting” or simply goes quiet. Retail holders are left with worthless bags.
How Every Metric Gets Manipulated
The most sophisticated aspect of long pump-and-dump schemes is the systematic manipulation of every metric that retail investors use to evaluate projects. Understanding that these metrics can be manufactured is essential to avoiding the trap.
Token holder count. Freshly-created wallets holding dust amounts (tiny token quantities) are generated in bulk to inflate holder counts. A project with “50,000 holders” may have 45,000 wallets that hold $0.10 worth of tokens — created specifically to make the holder metric impressive. This is exactly what ChainAware Token Rank detects: by measuring the quality of holders (via Wallet Rank), it reveals whether a token’s holder base consists of genuine investors or manufactured dust wallets.
Trading volume. Market makers can execute wash trades — buying and selling between controlled wallets — to generate artificial volume that makes the token appear more actively traded than it is. High volume on a small-cap token is often a manipulation signal rather than organic interest.
Social media followers and engagement. Twitter/X followers, Telegram members, Discord members, and engagement metrics are all purchasable in bulk. A project with 100,000 Twitter followers and 50,000 Telegram members may have genuine community reach of 3,000 people — the rest are purchased accounts, bots, or inactive members seeded in the early days.
Technical analysis patterns. More sophisticated operations actually engineer specific price chart patterns that trigger retail technical analysis signals — knowing that many retail investors act on TA patterns like golden crosses, breakouts, and support bounces. The market maker creates the pattern; retail traders follow the signal; insiders sell into the resulting buying pressure.
Partnership announcements. “Partnership” announcements in crypto are frequently MOUs (non-binding memoranda of understanding) or marketing relationships rather than substantive technical or commercial integrations. Each announcement generates buying pressure that is sold into. As examined in our crypto marketing guide, the appearance of momentum is itself a manufactured product in these schemes.
See Through Manufactured Token Communities
Token Rank: Genuine Holders vs Bot/Dust Wallets
Token Rank measures the median Wallet Rank of all token holders — not just the count. A token held by genuine, experienced Web3 participants ranks high. A token stuffed with dust wallets and farming bots ranks low. The metric that manufactured communities cannot fake.
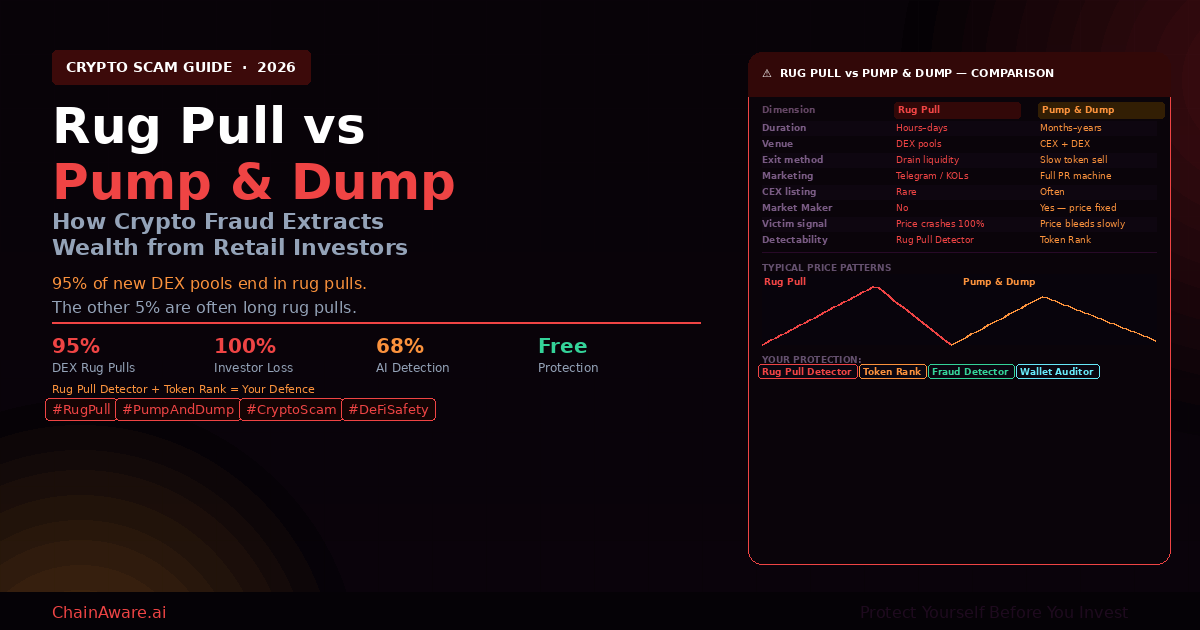
Rug Pull vs Pump and Dump: Side-by-Side
| Dimension | Rug Pull | Pump & Dump (Long Rug) |
|---|---|---|
| Duration | Hours to days | Months to years |
| Primary venue | DEX pools only | CEX listings + DEX |
| Exit mechanism | Drain liquidity or mint & sell | Continuous drip selling |
| Market maker | Rarely | Always — central to scheme |
| Marketing scale | Telegram/KOL burst | Full PR machine, ongoing |
| Victim signal | Sudden 100% price crash | Slow price bleed with pumps |
| Fake metrics used | Telegram members, price | Holders, volume, followers, TA patterns |
| Best detector | Rug Pull Detector | Token Rank |
The Real Damage: Why This Limits All of Crypto
The financial losses from rug pulls and pump-and-dump schemes are enormous and well-documented. But the deeper damage is structural: these scams are systematically driving new crypto enthusiasts out of the sector.
The pattern repeats continuously: a new person discovers crypto. They’re excited about the technology, the potential, the community. They invest in a project that looks legitimate. They get rug pulled or slowly dumped on. They lose most or all of their investment. They conclude that crypto is a scam — not just this token, but the entire sector — and they leave, permanently.
Meanwhile, the fraud industry’s operators extract their profits and launch the next project. They earn. The sector loses a potential long-term participant. Multiply this by millions of people globally, and the cumulative effect is a crypto sector that struggles to retain new users beyond the initial excitement phase — because the initial experience for too many participants is being defrauded.
As noted in the Immunefi Web3 security report, exit scams and rug pulls account for a growing share of total crypto losses annually — and unlike technical hacks (which drive security improvements), social engineering fraud drives users away entirely.
The solution is not to discourage crypto participation. It is to equip participants with the tools to distinguish genuine projects from fraud operations before they invest — which is exactly what the protection tools below do.
Protection 1: ChainAware Rug Pull Detector
The ChainAware Rug Pull Detector is your first line of defense against DEX pool fraud. Before adding any liquidity to a new pool, paste the contract address into the Rug Pull Detector and get an immediate risk score.
The tool works by analyzing the Trust Scores of the contract creator and major liquidity providers — not by reading smart contract source code (which can be obfuscated or unavailable). Its core logic: trustworthy pools are created by verified, established actors. Rug pull pools are almost always created by new addresses, low-trust addresses, or addresses deliberately obscuring their identity. A 68% accuracy rate from pure behavioral analysis — no code inspection required — represents a substantial improvement over investing blind.
Key red flags the Rug Pull Detector identifies: new contract creator address (freshly created wallets are the #1 rug pull signal); low Trust Score on the creator; new or low-trust LP addresses (LPs are the exit mechanism in liquidity drain rugs); and hidden creator chains (deployment routed through multiple intermediate contracts to obscure the ultimate actor).
For the complete technical guide, see our Rug Pull Detector guide.
Protection 2: ChainAware Token Rank
Token Rank is the primary defense against pump-and-dump schemes — specifically against the manufactured community metrics that make long rug pulls look legitimate.
The ChainAware Token Rank measures the median Wallet Rank of all token holders — not just the count. This is the key insight: you cannot fake quality. You can buy 50,000 dust wallets in a day, but those wallets will have near-zero Wallet Ranks — new addresses with no transaction history, no protocol interactions, no behavioral depth. Genuine token holders — experienced DeFi participants who chose this token based on their own research — will have high Wallet Ranks reflecting years of legitimate on-chain activity.
Token Rank is therefore a direct implementation of swarm intelligence: the collective judgment of thousands of experienced Web3 participants. If a token has a high Token Rank, it means many high-quality wallets chose to hold it — a signal that is much harder to manufacture than follower counts or volume metrics.
Before investing in any token — especially a new or trending one — check its Token Rank. A high rank is an indicator of genuine community. A low rank, regardless of what the headline metrics show, signals a holder base that is primarily manufactured. Full explanation in the Token Rank complete guide.
Verify Counterparties Before You Trade
Fraud Detector + Wallet Auditor: Know Who You’re Dealing With
98% accurate fraud prediction for any wallet address. Plus full behavioral profiles: experience, risk willingness, intentions, AML status. Check team wallets, KOLs, large holders, and any counterparty before you transact.
Protection 3: ChainAware Fraud Detector
While the Rug Pull Detector protects against pool-level risk and Token Rank protects against token-level manipulation, the ChainAware Fraud Detector protects at the individual address level — answering the question: is this specific wallet trustworthy?
Use the Fraud Detector to verify team wallets before investing in any project. If the project’s deployer address or treasury address has a low Trust Score, that is a direct red flag regardless of what the project’s marketing says. Use it to check large token holders (“whales”) whose sell behavior could impact your position. Use it to verify the addresses of KOLs promoting a project — their on-chain history either confirms or contradicts their claimed expertise. And use it before any payment to a service provider, partner, or counterparty you’ve met through Telegram or Discord.
At 98% prediction accuracy and completely free, running a Fraud Detector check before any significant financial decision in crypto is one of the highest-ROI security practices available. Full guide: ChainAware Fraud Detector complete guide. For a broader explanation of why Trust Scores matter so much in crypto: Why Crypto Trust Score Metrics Are Important.
Protection 4: Other Tools Worth Using
ChainAware provides the most comprehensive behavioral intelligence stack, but a complete protection posture includes several complementary tools from across the ecosystem:
Token Sniffer (tokensniffer.com). Automated smart contract analysis that scans for known rug pull code patterns, similarity to previous scam contracts, and dangerous contract functions like unlimited minting or trading restrictions. Free. Useful as a quick first pass on any new token contract before the Rug Pull Detector’s deeper behavioral analysis.
De.Fi Shield. Protocol-level risk scoring that rates DeFi projects on smart contract security, team transparency, and operational track record. Particularly useful for evaluating established protocols rather than brand-new token launches.
Etherscan / BscScan verified contract check. Before interacting with any contract, verify it on the relevant block explorer. Unverified contracts are an immediate red flag. Check the deployer address’s transaction history directly on the explorer — a deployer with a history of previous token deployments that went to zero is a pattern that should stop any investment decision.
Bubblemaps (bubblemaps.io). Visualizes token holder concentration and wallet clusters — revealing whether a small number of connected wallets control a disproportionate share of supply. High concentration in a small cluster of connected wallets is a strong pump-and-dump signal.
DeFiLlama. Provides TVL (Total Value Locked) data for DeFi protocols. A protocol’s TVL trend is one metric that is harder to fake at scale than social metrics — though sophisticated operations can temporarily inflate TVL through connected wallets providing and withdrawing liquidity strategically.
DYOR: The Framework That Never Fails
“Do Your Own Research” has become a meme in crypto — sometimes used sarcastically when a project fails, as if research could have prevented the loss. But genuine DYOR, applied systematically, does prevent most losses. Here is the framework:
Check the contract and deployer. Who deployed this contract? How old is the deployer wallet? What is its Fraud Detector Trust Score? Has it deployed other contracts, and what happened to them? These questions take less than 5 minutes and filter out the vast majority of obvious rug pulls.
Check the token holder quality. Run Token Rank. Look at the top holders on the block explorer. Are the large holders established wallets with long histories, or fresh addresses created in the last few weeks? A token where the top 10 holders are all freshly-created wallets is a red flag regardless of what the project says about its community.
Check the liquidity situation. Is the liquidity locked? For how long? Who are the LPs? Run the pool through the Rug Pull Detector. Unlocked liquidity controlled by anonymous new wallets is the technical setup for a liquidity drain rug pull.
Question the narrative. Does the “10x guaranteed” or “100x potential” language trigger your skepticism? It should. Legitimate projects describe their product, their market, and their competitive position — they don’t promise returns because they can’t know their returns. Return promises are a feature of fraud operations, not investments.
Verify the team’s on-chain presence. Does the team have verifiable on-chain histories that match their claimed backgrounds? A DeFi team claiming years of experience whose wallets were created 3 months ago is a contradiction. The Wallet Auditor verifies exactly this.
For a comprehensive framework covering all Web3 investment and security practices, see our ChainAware complete product guide.
ChainAware.ai — Complete Anti-Fraud Stack
Don’t Invest Before You Check. It’s Free. It Takes Seconds.
Rug Pull Detector for pools. Token Rank for token quality. Fraud Detector for wallet addresses. Wallet Auditor for full profiles. Everything you need to distinguish genuine opportunities from the 95% that aren’t.
Frequently Asked Questions
What is the difference between a rug pull and a pump and dump?
A rug pull is a fast exit scam — the team drains liquidity or mints and sells tokens in hours to days, collapsing the price to zero immediately. A pump and dump (“long rug pull”) is a slow exit over months to years — insiders gradually sell into manufactured retail buying pressure while maintaining the appearance of a legitimate project. Both result in near-total investor losses; the difference is speed and sophistication.
Why do 95% of PancakeSwap pools end in rug pulls?
Because launching a rug pull token on a DEX requires minimal capital, zero identity verification, and takes minutes. The barrier to entry for fraud is essentially zero — making it a high-return, low-risk operation for scammers. The 95% figure reflects the reality that most new token launches on high-activity DEX chains are fraud operations, not legitimate projects.
How does the Rug Pull Detector work?
It analyzes the Trust Scores of the contract creator and liquidity providers using ChainAware’s behavioral AI — not smart contract source code. A pool where the creator and LPs are new or low-trust addresses is flagged as high risk. 68% accuracy without any code analysis. Free to use. Full guide: Rug Pull Detector guide.
What does Token Rank measure and why does it detect pump-and-dump schemes?
Token Rank measures the median Wallet Rank of all token holders — the collective quality of everyone holding the token. Pump-and-dump schemes inflate holder counts with dust wallets that have near-zero Wallet Ranks. Token Rank reveals this inflation: a token with 50,000 holders but a very low Token Rank has manufactured its community. A token with a high Token Rank has genuine, experienced holders who chose it voluntarily.
Can I use these tools before investing on a CEX-listed token?
Yes. Token Rank and the Fraud Detector work on any token address regardless of whether it’s DEX or CEX-listed. For CEX-listed tokens, Token Rank is particularly valuable for detecting the manufactured holder metrics that pump-and-dump schemes use to justify their exchange listings. Check the token contract address directly rather than relying on the exchange’s listing as a legitimacy signal.
Is DYOR really enough to protect against sophisticated scams?
DYOR is necessary but not sufficient on its own — that’s why the specific tools above exist. Sophisticated pump-and-dump operations are specifically designed to pass surface-level DYOR. The tools — Rug Pull Detector, Token Rank, Fraud Detector — analyze signals that are not visible to casual research: behavioral patterns, holder quality, creator Trust Scores. Use DYOR as the framework and these tools as the instruments within it.