DAO treasuries now hold $21.4 billion in liquid assets. Governance attacks have already stolen hundreds of millions — $181 million from Beanstalk in a single transaction, $150 million from The DAO before that. Average voter turnout sits at just 17% across DAOs in 2025, meaning an attacker needs far fewer tokens than most participants assume to capture a vote. The top ten voters in Uniswap and Compound already control between 45% and 58% of all voting power. Meanwhile, 60% of DAO proposals lack any consistent code disclosure. The governance attack surface in Web3 is enormous, poorly understood, and underscreened.
This 2026 guide maps the seven most important Web3 governance screeners — covering proposal tracking, participant behavioral screening, on-chain anomaly detection, and Sybil resistance. Together, these tools address the three questions every DAO participant should ask before engaging with any governance action: Who are the people behind this proposal? Is this proposal what it claims to be? Are anomalous voting patterns accumulating that signal an attack in progress?
In This Guide
- The Governance Attack Landscape in 2026
- The Three Screening Layers Every DAO Needs
- 1. ChainAware.ai — Behavioral Participant Screening
- 2. Tally — On-Chain Governance Execution and Delegate Analytics
- 3. DeepDAO — Participant Reputation and Treasury Analytics
- 4. Messari Governor — Proposal Importance Scoring and Sentiment Analysis
- 5. Snapshot — Off-Chain Voting and Misconfiguration Risks
- 6. Hypernative — Real-Time On-Chain Anomaly Detection
- 7. Gitcoin Passport — Sybil Resistance and Voter Identity
- Head-to-Head Comparison Table
- The Three-Layer Governance Defense Stack
- FAQ
The Governance Attack Landscape in 2026
Governance attacks differ fundamentally from other Web3 security threats. A smart contract exploit requires technical skill to find and execute a vulnerability. A rug pull requires a fraudulent operator to build a fake project. A governance attack, by contrast, exploits the legitimate decision-making mechanism of a protocol — using voting rights to pass proposals that drain treasuries, grant excessive privileges, or implement backdoor logic. The attack is often entirely “legal” from the protocol’s perspective: it follows the rules as written. The problem is that those rules were designed for participants acting in good faith, and they fail catastrophically when an adversarial actor accumulates sufficient voting power.
How Governance Attacks Happen
Three primary attack vectors dominate the governance attack landscape in 2026. First, flash loan governance capture — the Beanstalk attack pattern. An attacker uses DeFi flash loans to borrow enormous quantities of governance tokens instantaneously, cast votes on a malicious proposal in the same transaction block, and repay the loans before any defense is possible. Beanstalk’s emergencyCommit function required no timelock between voting and execution — allowing the attacker to propose, vote, and drain $181 million in a single block. Second, slow accumulation Sybil attacks — the patient version. An attacker creates dozens or hundreds of wallets, accumulates governance tokens across all of them over months, behaves as normal community participants, and then activates all wallets simultaneously when voter turnout is low enough to achieve a quorum with minority capital. Third, obfuscated proposal attacks — proposals that appear benign or routine but contain hidden logic in their execution payload. As documented by Cantina’s governance attack research ↗, more than 60% of DAO proposals lack consistent code disclosure, making malicious execution payloads difficult to detect. For how behavioral patterns identify these threats before execution, see our AI-Based Predictive Fraud Detection guide.
Why Existing Tools Miss the Most Dangerous Attacks
The governance security tooling that exists today addresses the wrong layers. Smart contract audits (Certik, Trail of Bits, OpenZeppelin) check governance contract code before deployment — they cannot prevent an attacker from legitimately acquiring enough tokens to capture a correctly-written contract. Post-attack forensics tools (Chainalysis, TRM Labs) document losses after the fact — they do not prevent them. The missing layer is real-time behavioral screening of the wallets that actively participate in governance. A wallet accumulating governance tokens across 40 fresh addresses, interacting with known flash loan infrastructure, or holding fraud patterns from previous scam operations carries all of that history permanently on-chain. No governance platform currently reads that history before allowing proposal creation, delegation, or vote casting. That gap is exactly what ChainAware addresses. For the complete comparison between reactive forensics and predictive behavioral intelligence, see our Forensic vs AI-Powered Blockchain Analysis guide.
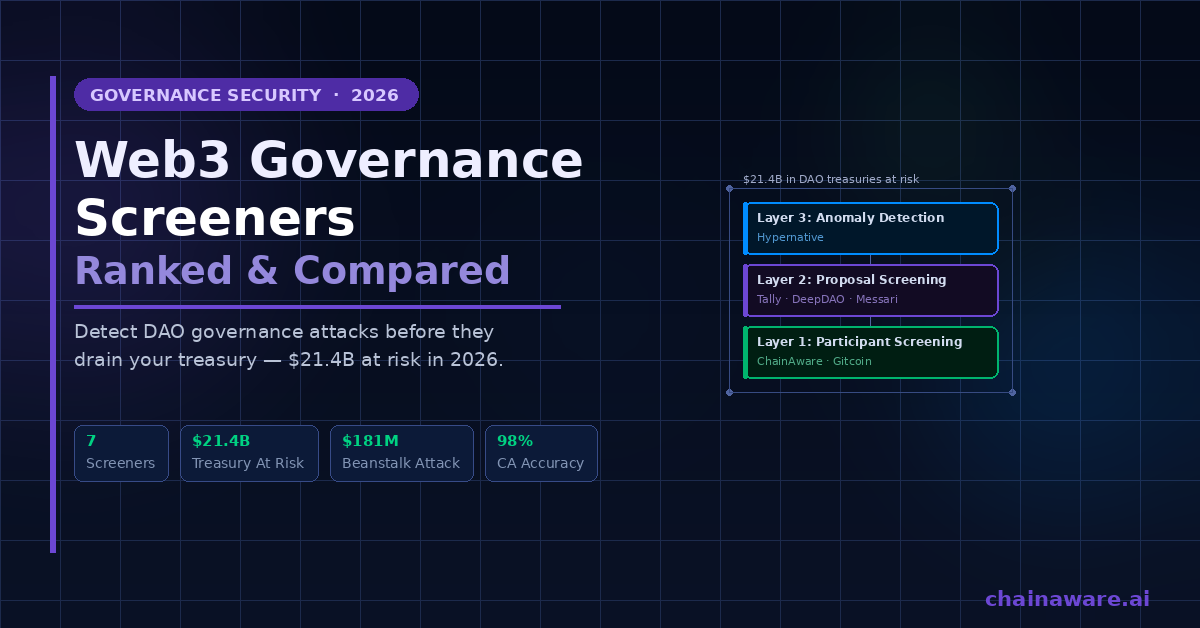
The Three Screening Layers Every DAO Needs
Effective governance security requires tools operating at three different points in the governance lifecycle. Layer 1 is participant screening — verifying the behavioral history of wallets creating proposals, accumulating voting power, and acting as delegates before they gain influence. Layer 2 is proposal screening — evaluating whether proposals are what they claim to be, flagging unusual importance levels, tracking community sentiment, and identifying obfuscated execution payloads. Layer 3 is anomaly monitoring — detecting unusual patterns in token accumulation, voting bloc formation, and governance contract interactions that signal an attack in progress. The seven tools in this comparison address different combinations of these three layers. Only one of them — ChainAware — addresses Layer 1 directly. For the broader context of how behavioral AI protects Web3 infrastructure, see our Web3 Agentic Economy guide and our AI-Powered Blockchain Analysis guide.
1. ChainAware.ai — Behavioral Participant Screening
Core function: Predict the fraud probability and behavioral profile of any wallet involved in governance — proposal creators, large token holders, delegates, and flash loan infrastructure users.
ChainAware fills the governance security gap that every other tool in this comparison leaves open. Rather than analyzing the governance contract code or tracking proposal metadata, ChainAware analyzes the on-chain behavioral history of the wallets participating in governance. This matters because governance attacks do not originate in the smart contract — they originate in the behavior of the humans accumulating voting power. A wallet that has previously participated in rug pull operations, interacted with known flash loan attack infrastructure, been involved in coordinated Sybil-pattern distributions, or carried fraud indicators across previous on-chain activity carries all of that history permanently on-chain, ready to be read.
Practical Governance Screening with ChainAware
The application is straightforward. When a new proposal appears in your DAO, paste the proposal creator’s wallet address into ChainAware’s Fraud Detector. If the creator has a high fraud probability score, that is a serious red flag regardless of how legitimate the proposal text appears. Similarly, when a new delegate or large token holder emerges in your DAO — especially one accumulating tokens rapidly from multiple addresses — audit those wallet addresses through ChainAware’s Wallet Auditor to assess their behavioral profile, experience level, and risk indicators. This check takes under a second per address, costs nothing for individual queries, and provides the only behavioral signal available about who that person actually is behind the anonymity of a blockchain address.
Furthermore, ChainAware’s Prediction MCP enables DAOs to automate this screening at scale. AI agents integrated via the MCP can query fraud scores and behavioral profiles for every address that interacts with a governance contract in real time — flagging suspicious participants before they accumulate enough voting power to be dangerous. This is the governance equivalent of Know Your Customer (KYC) that preserves on-chain anonymity while still providing meaningful behavioral risk signals. For the full Prediction MCP integration guide, see our Prediction MCP guide and our 12 Blockchain Capabilities Any AI Agent Can Use guide.
Governance use cases: Proposal creator screening · Delegate fraud history audit · Large token holder behavioral profiling · Sybil wallet cluster detection · Flash loan infrastructure interaction history
Chains: ETH, BNB, BASE, HAQQ
Free tier: Yes — individual wallet checks at chainaware.ai
API/MCP: Yes — Prediction MCP for automated governance screening
Limitation: Fresh wallets with no transaction history provide limited signal — combine with Hypernative for real-time accumulation monitoring
Screen Any Governance Participant in 1 Second
ChainAware Wallet Auditor — Behavioral Profile on Any Proposer or Delegate
Before you vote on a proposal or delegate your tokens, audit the wallet behind it. ChainAware shows fraud probability, experience level, risk profile, and behavioral history for any address — in under a second, free, no wallet connection. The governance security check every DAO participant should run.
2. Tally — On-Chain Governance Execution and Delegate Analytics
Core function: On-chain voting interface and proposal execution for OpenZeppelin Governor DAOs — with transparent voting records, delegate profiles, and cross-chain governance coordination.
Tally is the leading execution layer for on-chain DAO governance in 2026. The platform raised an $8 million Series A in April 2025 — explicitly to address low voter participation and introduce staking mechanisms that reward active governance participants. Today, Tally secures governance for protocols managing over $30 billion in assets, including Arbitrum, Uniswap, ZKsync, EigenLayer, Wormhole, Obol, and Hyperlane. Usage grew 45% in 2025 as regulatory clarity in the US drove renewed institutional interest in structured DAO participation.
Governance Screening Value in Tally
Tally provides meaningful governance screening capability through its transparent voting infrastructure. Every vote cast on every proposal is permanently recorded on-chain, enabling any participant to see exactly how any delegate has voted across all proposals in a DAO’s history. This voting record transparency is governance accountability that no off-chain system can fake — if a delegate claims to vote in the community’s interest but their on-chain record shows consistent votes favoring insider proposals, that pattern is visible. Additionally, Tally’s delegate profile pages aggregate voting history, participation rates, and rationale statements, giving token holders the information to make informed delegation decisions. For context on how on-chain transparency enables the behavioral analysis that ChainAware builds on, see our Generative vs Predictive AI guide.
Tally’s primary limitation from a security screening perspective is that it provides historical voting transparency but does not predict future behavior. It shows what delegates have voted for; it does not tell you whether those delegates have off-governance fraud histories or whether they have been coordinating wallet accumulation outside the platform. That pre-participation behavioral layer requires ChainAware as a complement.
Governance screening value: Voting history transparency · Delegate accountability · Proposal lifecycle tracking · Cross-chain governance coordination
Chains: Ethereum and EVM L2s
Free tier: Yes for participation; institutional features priced separately
Best for: On-chain Governor DAOs requiring full execution accountability and delegate analytics
3. DeepDAO — Participant Reputation and Treasury Analytics
Core function: The broadest DAO analytics platform — 2,500+ DAOs, 11 million governance participant profiles, $21.4 billion in treasury tracking, and wallet-level governance reputation by ENS name or address.
DeepDAO provides the most comprehensive governance participant database available in Web3. Founded in Tel Aviv in February 2020, the platform emerged from a direct observation gap: Eyal Eithcowich, participating in Genesis Alpha DAO, wanted to see voting patterns and proposal creators but found no tools that provided this view. DeepDAO has since grown to track 13,000+ DAOs globally, 6.5 million governance token holders, and $21.4 billion in liquid treasury assets across protocols on Ethereum, Polygon, Optimism, Arbitrum, Gnosis Chain, and expanding networks.
Participant Reputation Profiles as Governance Screening
DeepDAO’s most relevant governance screening feature is its participant profile system. Any DAO member can search by wallet address or ENS name and see that address’s complete governance history — all DAO memberships, every proposal created, every vote cast, and treasury contributions across all tracked protocols. This cross-DAO reputation view is powerful for screening because it shows whether a new participant in your DAO has a history of legitimate, sustained governance engagement elsewhere, or whether they appear to have no meaningful governance history at all despite holding significant tokens. A whale voter who suddenly appears with large token holdings and zero prior governance engagement across 2,500 DAOs is a significant anomaly worth investigating further. For broader context on how participant behavioral history connects to security, see our AI-Based Wallet Audit guide.
DeepDAO’s limitation as a security screener is that its participant profiles cover governance activity only — not broader on-chain behavioral history. A wallet might have zero governance history in DeepDAO’s database while having a rich fraud history visible in ChainAware’s behavioral models. The two tools are therefore complementary: DeepDAO shows governance-specific reputation; ChainAware shows full on-chain behavioral fraud probability.
Governance screening value: Cross-DAO participant reputation · Treasury analytics · Proposal and voting history · New participant background assessment
Coverage: 2,500+ DAOs, 11M profiles, EVM chains
Free tier: Yes; Pro and API tiers for advanced access
Best for: Due diligence on delegates and large token holders; DAO ecosystem analysis
Screen Governance at Platform Scale
ChainAware Prediction MCP — Automate Governance Participant Screening
DAOs managing significant treasuries need automated participant screening, not manual checks. ChainAware’s Prediction MCP lets any AI agent query fraud scores and behavioral profiles for governance participants in real time — via natural language or REST API. Flag risky proposers and suspicious token accumulators before they reach quorum. 18M+ wallet profiles. 8 blockchains.
4. Messari Governor — Proposal Importance Scoring and Sentiment Analysis
Core function: Proposal aggregation across 800+ DAOs with AI-powered importance scoring, community sentiment analysis, governance alerts, and full proposal lifecycle tracking from forum discussion to on-chain execution.
Messari Governor addresses a specific and underappreciated governance security problem: information overload. A serious DAO participant tracking multiple protocols simultaneously faces dozens of proposals per week, the majority of which are routine and low-stakes. The inability to quickly distinguish a routine parameter adjustment from a high-risk treasury reallocation or a potentially malicious upgrade proposal is itself a security vulnerability — it creates the exact conditions of voter fatigue and low participation that governance attackers exploit.
Importance Scoring and Sentiment as Security Signals
Messari Governor’s importance scoring system classifies proposals by severity — Low, Medium, High, and Very High — based on the nature of the action proposed, the treasury value at stake, and the scope of protocol changes involved. This classification enables governance participants to prioritize their attention on proposals that genuinely warrant deep scrutiny, rather than spending equal time reviewing routine operational decisions. The sentiment analysis feature adds a second signal: by analyzing community discussion patterns in forums and on-chain voting trends, Messari produces an objective probability estimate of whether each proposal is likely to pass.
From a security screening perspective, these features provide a meaningful early-warning layer. A proposal classified as High or Very High importance that simultaneously carries unusual community sentiment patterns — for example, rapid forum support appearing from new accounts, or voting momentum inconsistent with normal participation patterns — warrants additional scrutiny of the wallets driving that momentum. Messari Governor currently tracks over 5,000 proposals from hundreds of DAOs, with customizable governance alerts deliverable via email or platform notification. For how AI-powered analysis of governance activity connects to broader behavioral intelligence, see our Real AI Use Cases guide.
Governance screening value: Proposal importance classification · Community sentiment analysis · Multi-DAO proposal aggregation · Governance alerts and notifications
Coverage: 800+ DAOs, 5,000+ proposals
Free tier: Limited; Pro and Enterprise tiers for full access
Best for: Professional governance participants and institutional delegates managing multiple DAOs simultaneously
5. Snapshot — Off-Chain Voting Infrastructure and Misconfiguration Risks
Core function: Gasless off-chain voting via cryptographic signatures stored on IPFS — the dominant voting platform for DAO governance with 96% market share.
Snapshot is not a governance screener — it is the governance voting infrastructure that most DAOs run on. Understanding it belongs in this guide because Snapshot’s own misconfiguration risks represent one of the most common and underappreciated governance security vulnerabilities in 2026. Chainalysis data shows that 17% of Snapshot voting configurations contain critical flaws — including allowing votes from tokens that users do not actually hold, quorum thresholds set so high that proposals routinely fail, or voting strategies that exclude staked token holders from participating. These misconfigurations create attack surfaces that sophisticated actors can exploit without any direct malicious action.
MiCA Compliance and the On-Chain Anchoring Requirement
Additionally, Snapshot’s off-chain architecture introduces a governance security concern that is receiving increasing regulatory attention. Because Snapshot votes are not recorded on-chain, they have no automatic enforcement mechanism — someone must manually execute approved proposals through a multisig or Gnosis Safe. If the multisig signers collude or disappear, an approved vote has no effect. Snapshot’s November 2025 release of Spaces 2.0 — enabling custom domains like vote.yourdao.eth — improves branding and phishing resistance but does not solve the execution trust problem. More significantly, the EU’s MiCA regulation requires DAOs with over €5 million in assets to anchor off-chain votes on-chain by Q2 2026, forcing a significant portion of the Snapshot ecosystem to adopt hybrid execution models. For how MiCA compliance requirements intersect with behavioral transaction monitoring, see our AML and Transaction Monitoring guide and our Blockchain Compliance guide. For the official MiCA framework, see the ESMA MiCA documentation ↗.
Governance screening value: Voting strategy verification (avoid misconfiguration) · Vote record accessibility · Community signaling layer
Coverage: 96% of major DAOs, 52+ blockchain networks
Free tier: Yes — free for DAOs and participants
Best for: Off-chain signaling, gasless voting; requires companion tools for security screening and execution
6. Hypernative — Real-Time On-Chain Anomaly Detection
Core function: Proactive, real-time security and risk monitoring platform for Web3 — detects on-chain anomalies, governance contract interactions, and flash loan preparatory behavior across 50+ chains before attacks execute.
Hypernative addresses the most time-critical governance security problem: detecting an attack in progress fast enough to respond before it executes. The Beanstalk attack succeeded in part because the malicious proposal’s true nature was not identified until after the flash loans had been taken and the governance function called — a window of minutes or less. Traditional governance monitoring (checking the Tally interface, reading forum discussions) operates on human timescales completely inadequate for blocking same-block governance attacks.
Pre-Attack Signal Detection at Machine Speed
Hypernative monitors governance contract interactions in real time, tracking unusual patterns in token accumulation, voting bloc formation, and flash loan preparatory transactions that typically precede governance attacks. When anomalous behavior exceeds configured risk thresholds, Hypernative delivers alerts to designated contacts within seconds — giving security teams the window to activate emergency mechanisms, contact multisig holders, or pause contracts before irreversible damage occurs. The platform operates at enterprise scale and integrates with incident response workflows used by professional security teams, making it most relevant for DAOs managing significant treasury assets with dedicated security resources. For how real-time monitoring connects to the broader Web3 security stack, see our Web3 Fraud Detection guide.
Governance screening value: Real-time governance anomaly detection · Flash loan preparatory behavior alerts · Token accumulation monitoring · Incident response integration
Chains: 50+ chains
Free tier: No — enterprise B2B pricing
Best for: High-value protocol DAOs with dedicated security teams and >$10M treasury exposure
Limitation: Enterprise pricing makes it inaccessible for smaller DAOs and individual participants
7. Gitcoin Passport — Sybil Resistance and Voter Identity
Core function: Web3 identity aggregation across multiple platforms and credentials — enabling Sybil-resistant governance by giving participants verifiable identity scores that reflect genuine human activity.
Gitcoin Passport solves the governance identity problem that token-weighted voting cannot address: verifying that votes come from genuine, unique human participants rather than coordinated networks of wallet addresses controlled by a single actor. Standard token-weighted voting treats every wallet identically regardless of whether it represents a human being or one of forty sockpuppet accounts operated by the same attacker. Quadratic voting attempts to reduce whale power by making each additional vote exponentially more expensive — but as academic research from Stanford has demonstrated, quadratic voting systems are vulnerable to Sybil attacks where the attacker simply creates enough wallets to negate the quadratic cost penalty.
Passport Score as Governance Admission Screening
Gitcoin Passport aggregates verifiable credentials from sources including ENS domain ownership, POAP attendance records, GitHub activity, Twitter verification, and multiple Web3 protocol interactions — generating a composite Passport score that reflects the breadth of a participant’s genuine on-chain and off-chain activity. DAOs using quadratic voting or other Sybil-sensitive mechanisms can require minimum Passport scores for proposal submission or voting participation, effectively screening out fresh wallets with no verifiable history. This complements ChainAware’s behavioral fraud screening: Passport verifies identity breadth while ChainAware checks fraud history depth. Together they address both sides of the participant legitimacy problem. For how on-chain behavioral history creates verifiable trust, see our Web3 Trust Verification guide and the Gitcoin Passport documentation ↗.
Governance screening value: Sybil-resistant voter identity · Quadratic voting protection · Proposal submission eligibility screening · Credential aggregation
Free tier: Yes — free for participants
Best for: DAOs using quadratic voting, grant DAOs, high-participation community governance
Limitation: Identity breadth only — does not detect fraud history; a high Passport score does not mean a wallet has no fraud behavioral patterns
Add Fraud Behavioral Intelligence to Your Governance Stack
ChainAware Fraud Detector — Check Any Proposer Wallet in 1 Second
Tally shows vote history. DeepDAO shows governance reputation. Gitcoin shows identity breadth. ChainAware shows fraud probability — the on-chain behavioral history that no other governance tool reads. Free. Real-time. 98% accuracy backtested on CryptoScamDB. ETH, BNB, BASE, HAQQ.
Head-to-Head Comparison Table
| Tool | Screening Layer | Checks Fraud History? | Real-Time? | Coverage | Free? | Best For |
|---|---|---|---|---|---|---|
| ChainAware.ai | Layer 1: Participant behavioral fraud prediction | ✅ Core differentiator | ✅ Sub-second | ETH, BNB, BASE, HAQQ | ✅ | Screening proposers, delegates, accumulating wallets |
| Tally | Layer 2: On-chain vote execution + delegate history | ❌ No fraud history | ✅ | Ethereum + EVM L2s | ✅ | Governor DAOs needing execution accountability |
| DeepDAO | Layer 2: Cross-DAO governance reputation | ❌ Governance history only | ✅ | 2,500+ DAOs, EVM | ✅ (limited) | Participant background across DAOs |
| Messari Governor | Layer 2: Proposal importance + sentiment | ❌ | ✅ Alerts | 800+ DAOs | Limited | Multi-DAO proposal screening for delegates |
| Snapshot | Voting infrastructure (screening via config audit) | ❌ | ✅ | 96% of DAOs | ✅ | Off-chain signaling; verify voting strategy config |
| Hypernative | Layer 3: Real-time on-chain anomaly detection | Partial (anomaly patterns) | ✅ Machine speed | 50+ chains | ❌ Enterprise | High-value DAOs with security teams |
| Gitcoin Passport | Layer 1: Voter identity / Sybil resistance | ❌ Identity breadth only | ✅ | Web3 multi-chain | ✅ | Quadratic voting DAOs, grant programs |
Governance Attack Type Coverage: What Each Tool Catches
| Attack Type | ChainAware | Tally | DeepDAO | Messari | Snapshot | Hypernative | Gitcoin |
|---|---|---|---|---|---|---|---|
| Flash loan governance capture | ✅ Flash loan infrastructure history | ❌ | ❌ | Partial | ❌ | ✅ Pre-attack signals | ❌ |
| Sybil multi-wallet accumulation | ✅ Behavioral cluster signals | ❌ | Partial (low history) | ❌ | ❌ | ✅ Token accumulation alerts | ✅ Identity scoring |
| Obfuscated malicious proposal | ✅ Creator fraud history | Partial (code visible) | Partial (creator history) | ✅ Importance + sentiment | ❌ | ✅ Anomalous support patterns | ❌ |
| Delegate bad faith voting | ✅ Delegate fraud behavioral history | ✅ Vote record transparency | ✅ Cross-DAO history | ✅ Sentiment analysis | ❌ | Partial | ❌ |
| Snapshot misconfiguration exploit | ❌ | ❌ | ❌ | ❌ | ✅ Config audit | ❌ | ❌ |
| Treasury drain via passed proposal | ✅ Proposer history pre-vote | ✅ Execution record | Partial | ✅ High importance flag | ❌ | ✅ Real-time execution monitoring | ❌ |
| Fraud operator as proposer | ✅ Only tool detecting this | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ |
The Three-Layer Governance Defense Stack
No single tool in this comparison provides complete governance security. Effective DAO governance protection requires tools operating across all three temporal phases of the governance lifecycle — before participants accumulate influence, while proposals are being created and voted on, and in real time as on-chain execution approaches. The following stack covers all three phases with the minimum tool overhead.
Layer 1: Screen Participants Before They Gain Influence
The most cost-effective governance security practice is screening participants before they reach meaningful voting power. When a new wallet begins accumulating governance tokens, when a new delegate registers on Tally, or when a new address submits a proposal — run that wallet through ChainAware’s Fraud Detector and Wallet Auditor immediately. Cross-reference governance-specific history in DeepDAO: does this address have any meaningful participation history across the DAO ecosystem, or did they appear with large token holdings and no prior governance engagement? For DAOs using quadratic voting, require a minimum Gitcoin Passport score for proposal submission to eliminate fresh Sybil wallets. These three checks take under five minutes total and close the participant legitimacy gap that every other governance security measure assumes has already been solved. For the complete participant screening workflow, see our ChainAware product guide and our AI-Based Wallet Audit guide.
Layer 2: Screen Proposals Before You Vote
Before casting any vote on a significant proposal, run a parallel check through Messari Governor for importance classification and community sentiment. High-importance proposals with unusual sentiment patterns warrant reading the full execution payload on Tally, not just the proposal summary. Verify the proposal creator’s wallet in ChainAware. Check whether major vote supporters are new wallets with no DeepDAO governance history. For Snapshot votes, audit the voting strategy configuration to verify it matches the DAO’s documented governance design — Chainalysis data shows 17% of Snapshot setups have critical flaws that sophisticated actors can exploit. According to research from a16z crypto’s governance attack analysis ↗, most successful governance attacks exploit a combination of low voter participation and inadequate proposal review — both preventable with Layer 2 screening practices.
Layer 3: Monitor in Real Time During Execution Windows
For high-value DAOs managing significant treasury assets, deploying Hypernative for real-time on-chain monitoring during proposal execution windows is the final layer. Governance timelocks — the 24-48 hour delays between vote approval and execution that protocols like Compound implement — provide the window during which anomalous behavior (flash loan preparation, rapid token accumulation, unusual contract interactions) can be detected and responded to before the proposal executes. This machine-speed monitoring layer is what Layer 1 and Layer 2 screening cannot provide: the ability to catch a sophisticated attacker who passed every pre-vote check but whose final execution preparation pattern reveals malicious intent. For how ChainAware’s transaction monitoring agent complements real-time governance surveillance, see our Transaction Monitoring guide. For the FATF regulatory framework that increasingly mandates transaction monitoring for VASPs including DAO protocols, see the FATF Virtual Assets Recommendations ↗.
Start With Free Analytics — Know Your DAO Participants
ChainAware Free Analytics — Behavioral Intelligence in 24 Hours
Before you can screen governance participants, you need behavioral visibility into who is actually connecting to your protocol. ChainAware Analytics delivers experience levels, risk profiles, and behavioral segment distributions for your connecting wallets — via 2-line GTM pixel. Free forever. The starting point for every governance security workflow.
Frequently Asked Questions
What was the Beanstalk governance attack and how could it have been prevented?
In April 2022, an attacker used flash loans to borrow $1 billion worth of assets, used those assets to buy enough governance tokens to hold a supermajority of voting power, and then called Beanstalk’s emergencyCommit function — which required a supermajority vote and had no timelock between voting and execution. The entire attack happened in a single transaction block. The $181 million drain was complete before any human could respond. Three design changes could have prevented it: a timelock between vote approval and execution (implemented by most modern Governor contracts), a flash loan protection mechanism that prevents tokens borrowed in the same block from voting, and a minimum holding period before governance tokens grant voting rights. ChainAware’s approach adds a fourth preventive layer: screening the behavioral history of the proposer wallet before the proposal is submitted — a fraudulent operator’s wallet history often contains signals of previous exploit infrastructure interactions.
How do Sybil attacks threaten DAO governance specifically?
A Sybil attack in DAO governance involves one actor creating many wallet addresses and distributing governance tokens across all of them to appear as multiple independent community members. Because voter participation in most DAOs sits at around 17%, an attacker controlling coordinated wallets holding even a modest percentage of total token supply can achieve quorum and pass proposals when genuine participation is low. The slow-accumulation version is particularly dangerous: wallets behave as normal community participants for months, never triggering governance alerts, until the attacker decides to activate all wallets simultaneously for a critical vote. Gitcoin Passport addresses this by requiring identity breadth verification. ChainAware complements this by detecting behavioral patterns in the accumulating wallets — mass token distributions from a single upstream source, wallet age inconsistencies, and interaction patterns that match known Sybil infrastructure.
What is the MiCA governance compliance requirement taking effect in 2026?
The EU’s Markets in Crypto Assets (MiCA) regulation requires DAOs with over €5 million in assets to anchor off-chain votes on-chain by Q2 2026. Currently, the majority of DAO voting happens through Snapshot — a gasless, off-chain system where votes are not recorded on-chain and have no automatic execution mechanism. MiCA’s on-chain anchoring requirement means these DAOs must implement hybrid execution systems (such as SafeSnap with Gnosis Safe) that cryptographically connect Snapshot vote outcomes to on-chain execution. This requirement increases governance transparency and auditability while also creating new implementation complexity that DAOs must manage carefully to avoid introducing new security vulnerabilities in the execution layer.
Why does governance screening require behavioral data rather than just governance history?
Governance history (available from Tally and DeepDAO) shows how a wallet has participated in DAO voting — which proposals it created, how it voted, which DAOs it belongs to. This is valuable for assessing reputation within the governance ecosystem. However, a sophisticated attacker deliberately builds a clean governance history over months of normal participation before executing an attack. Their governance history looks legitimate precisely because they designed it to. Behavioral fraud data (available from ChainAware) examines the wallet’s complete on-chain activity outside governance — DeFi interactions, token deployment history, relationship to known fraud infrastructure, behavioral consistency between claimed experience and actual transaction patterns. These signals are much harder to fake because they require genuine transaction cost and time investment across hundreds of interactions.
Which governance screener should small DAOs prioritize with limited resources?
Small DAOs with limited security resources should focus on the highest-impact, lowest-cost screening layer: participant behavioral checks using ChainAware (free for individual queries), combined with proposal importance monitoring via Messari Governor (free tier), and Snapshot voting strategy auditing (free, done once at setup). These three practices cover the most common governance attack vectors without requiring any enterprise tooling or dedicated security budget. Specifically, running every new proposal creator and every new large token holder through ChainAware’s Fraud Detector and Wallet Auditor is a five-minute routine that provides the most security leverage per unit of time of any governance screening practice available in 2026.
Sources: a16z Crypto — DAO Governance Attacks ↗ · Cantina — Governance as an Attack Vector ↗ · FATF Virtual Assets Recommendations ↗ · ESMA MiCA Documentation ↗ · Gitcoin Passport ↗