A hardware wallet is the most important security decision most crypto holders ever make. By keeping your private keys on an offline device that never connects directly to the internet, hardware wallets eliminate the largest single attack vector in crypto: the theft of private keys through malware, phishing, or exchange hacks. If you hold meaningful crypto and you don’t have a hardware wallet, this guide starts with the most important recommendation you’ll read today: get one.
But here is the truth that hardware wallet manufacturers don’t advertise: a hardware wallet alone is not enough to protect your funds.
Your hardware wallet protects your private keys. It does not protect you from sending those keys’ funds to a fraudulent address. It does not protect you from providing liquidity to a pool that rug pulls. It does not protect you from buying a token whose community is entirely fake. The hardware wallet signs whatever transaction you present to it — and if that transaction is moving your funds to a scammer, it will sign that too, faithfully and without complaint.
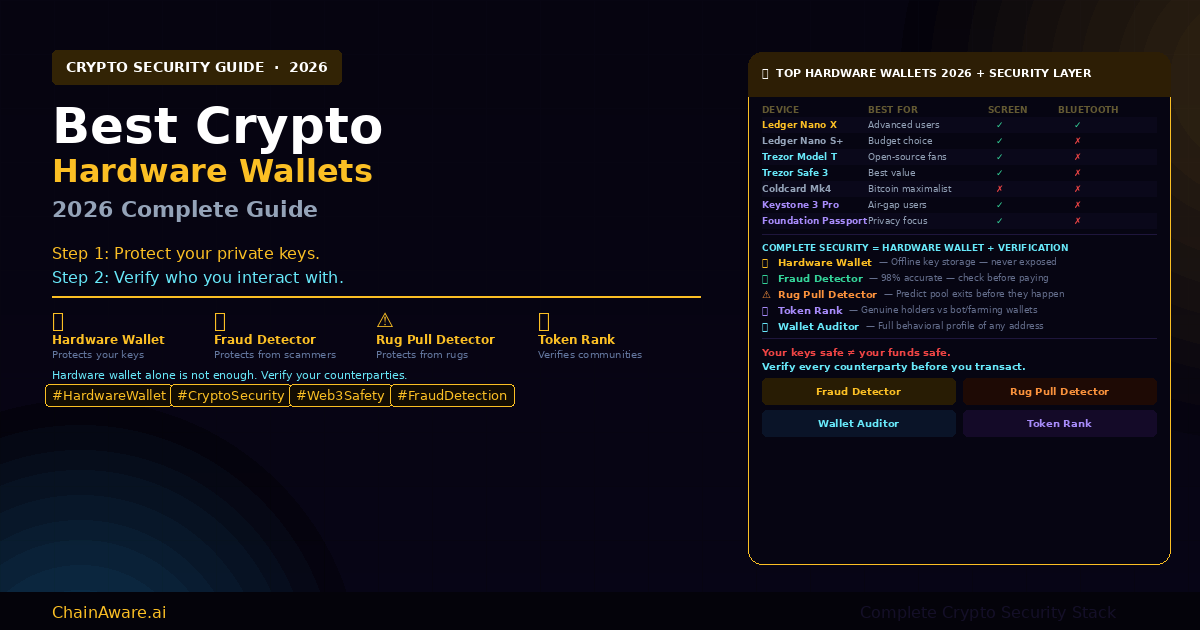
Complete crypto security in 2026 requires two layers: protecting your private keys (hardware wallet) and verifying the counterparties you interact with (Fraud Detector, Rug Pull Detector, Token Rank, Wallet Auditor). This guide covers both layers comprehensively.
What Is a Hardware Wallet and Why Do You Need One?
A hardware wallet is a physical device — roughly the size of a USB drive — that stores your cryptocurrency private keys in a secure offline environment. Your private key is the cryptographic secret that proves ownership of your crypto: whoever controls the private key controls the funds. Hardware wallets are designed around one core principle: the private key never leaves the device and never touches an internet-connected computer.
The alternative — storing private keys on a software wallet, a phone app, or an exchange — means the key exists in an environment where malware, phishing attacks, operating system vulnerabilities, and exchange hacks can potentially access it. The history of crypto is littered with billions of dollars lost through exactly these vectors.
Hardware wallets eliminate this risk by keeping the private key on a dedicated, isolated chip. When you want to sign a transaction, you connect the hardware wallet to your computer, approve the transaction on the device’s screen, and the signature is generated inside the device without the private key ever being transmitted. Even if your computer is fully compromised with malware, the attacker cannot extract your private key.
According to Chainalysis’s annual crypto crime report, exchange hacks and private key theft remain among the largest categories of crypto losses — all of which are prevented by hardware wallet usage. For anyone holding crypto beyond what they are willing to lose, a hardware wallet is a non-negotiable baseline security measure.
How Hardware Wallets Work
The security architecture of a hardware wallet has three key components.
Secure Element chip. Most hardware wallets use a dedicated Secure Element (SE) chip — the same technology used in credit cards, passports, and SIM cards — to store private keys. This chip is designed to be physically tamper-resistant and cryptographically isolated. Even if someone physically disassembles your hardware wallet, extracting the private key from a Secure Element chip requires equipment and expertise well beyond any casual attacker.
On-device transaction verification. The hardware wallet has its own screen — separate from your computer display — that shows the transaction details before you approve. This prevents a class of attacks where malware on your computer substitutes a different destination address in the transaction before it reaches the hardware wallet. What you see on the hardware wallet’s screen is what will be signed — not what your computer shows you.
Seed phrase backup. During setup, your hardware wallet generates a 12 or 24-word recovery phrase. This phrase is the master backup for your private key — anyone with this phrase can reconstruct your wallet. Store it offline, in multiple secure physical locations, and never photograph it or type it into any computer. The seed phrase is the one irreplaceable security element that hardware wallets cannot protect on your behalf.
Hardware Wallet Is Step 1 — Don’t Stop There
Check Every Address Before You Transact — 98% AI Accuracy
Your hardware wallet signs transactions. The Fraud Detector tells you whether the address you’re signing for is safe. Free. Real-time. Covers 8 networks. Run it before every payment to an unfamiliar address.
Best Crypto Hardware Wallets in 2026
The hardware wallet market has matured significantly. The choice is no longer simply Ledger vs Trezor — there are now strong options across multiple price points and use cases. Here is the complete breakdown of the best hardware wallets available in 2026.
Ledger Nano X and Nano S Plus
Ledger Nano X — Best Overall
The Ledger Nano X remains the most widely used hardware wallet in the world, and for good reason. It combines a Secure Element chip (CC EAL5+ certified), Bluetooth connectivity for mobile use, a clear OLED display, support for over 5,500 coins and tokens, and the mature Ledger Live software ecosystem — all in a compact device that fits in a pocket.
The Bluetooth feature, which allows connection to the Ledger Live mobile app without a USB cable, was controversial when introduced but has proven to be a practical convenience feature that does not compromise security — the private key never travels over Bluetooth, only the signed transaction does.
Best for: Active DeFi users and investors who want the most polished hardware wallet experience with broad ecosystem support.
Supported assets: 5,500+ coins and tokens
Price: ~$149
Key specs: Secure Element (CC EAL5+), Bluetooth, OLED display, USB-C
Ledger Nano S Plus — Best Budget Choice
The Nano S Plus offers the same Secure Element security as the Nano X at a lower price point — the trade-off being no Bluetooth and less internal storage (limiting simultaneous app installs, not the number of assets you can hold). For users who primarily manage a limited number of assets and don’t need mobile connectivity, the Nano S Plus delivers Ledger’s core security at an accessible price.
Best for: Budget-conscious holders who want genuine hardware security without premium features.
Price: ~$79
Key specs: Secure Element (CC EAL5+), USB-C, OLED display, no Bluetooth
Trezor Model T and Trezor Safe 3
Trezor Model T — Best for Open-Source Advocates
Trezor, created by SatoshiLabs, pioneered the hardware wallet market and remains the gold standard for open-source hardware security. Unlike Ledger, Trezor’s firmware is fully open-source — meaning the security community can (and does) audit the code independently. The Model T features a color touchscreen, support for thousands of coins, and integration with popular software wallets including MetaMask and Electrum.
The trade-off versus Ledger is that Trezor uses a general-purpose microcontroller rather than a dedicated Secure Element chip. Trezor’s security model relies on open-source auditability and physical tamper evidence rather than a proprietary secure enclave. For most users this is a non-issue; for users who prioritize hardware-level key isolation, the Secure Element architecture gives Ledger an edge.
Best for: Open-source advocates and users who prioritize community-audited security.
Price: ~$219
Key specs: Open-source firmware, color touchscreen, USB-C, no Bluetooth
Trezor Safe 3 — Best Value in 2026
The Trezor Safe 3 is SatoshiLabs’ answer to the cost-security trade-off: it introduces a Secure Element chip into Trezor’s open-source ecosystem for the first time, at a price point competitive with the Ledger Nano S Plus. This makes the Safe 3 arguably the best value hardware wallet in 2026 — combining Trezor’s trusted open-source firmware heritage with dedicated Secure Element protection.
Best for: Users who want the best of both worlds — open-source transparency and Secure Element protection — at a mid-range price.
Price: ~$79
Key specs: Secure Element, open-source firmware, compact design, USB-C
Coldcard, Keystone, Foundation Passport
Coldcard Mk4 — Best for Bitcoin Maximalists
Coldcard is the hardware wallet of choice for serious Bitcoin security practitioners. Designed exclusively for Bitcoin (no altcoin support), it offers the most advanced air-gap capabilities of any mainstream hardware wallet: it can sign transactions entirely offline via MicroSD card, never requiring a physical USB connection to a potentially compromised computer. The Mk4 also supports advanced multisig setups and has become the standard tool for high-security Bitcoin custody.
Best for: Bitcoin-only users who prioritize maximum operational security over convenience.
Price: ~$157
Key specs: Bitcoin-only, NFC, MicroSD air-gap signing, Secure Element, no display (buttons)
Keystone 3 Pro — Best Air-Gap Hardware Wallet
Keystone 3 Pro is a fully air-gapped hardware wallet — it has no USB data connection and communicates with software wallets exclusively through QR code scanning. This air-gap architecture means that even a USB-based attack vector is eliminated entirely. The large touchscreen and open-source firmware make it a practical daily-use device despite its uncompromising security model. Notably, Keystone integrates directly with MetaMask, making it an excellent choice for DeFi users.
Best for: DeFi power users who want air-gap security with MetaMask integration and a great user experience.
Price: ~$149
Key specs: Fully air-gapped (QR codes), 4-inch touchscreen, open-source firmware, three Secure Elements
Foundation Passport — Best for Privacy
Foundation Devices’ Passport is a premium Bitcoin hardware wallet built around open-source hardware (not just firmware — the hardware design files are publicly available) and maximum privacy. It communicates via QR codes or MicroSD, never USB, and is built in the United States. For users who want supply chain transparency and the highest level of open-source verification available, Passport is in a class of its own.
Best for: Privacy-focused Bitcoin holders and open-hardware advocates.
Price: ~$199
Key specs: Bitcoin-only, open-source hardware + firmware, QR/MicroSD air-gap, built in USA
95% of DeFi Pools End in Rug Pulls
Check Any Pool Before You Add Liquidity — Rug Pull Detector
Your hardware wallet won’t stop you from providing liquidity to a pool that exits. The Rug Pull Detector checks the Trust Scores of the contract creator and LPs — predicting rug pull risk before it happens. Free. No source code reading required.
Step 2: The Security Layer Hardware Wallets Can’t Provide
Your hardware wallet is doing its job perfectly when it faithfully signs a transaction that sends your USDC to a scammer. The private key was protected. The signature was valid. The transaction was irreversible. And your funds are gone.
This is the fundamental limitation that hardware wallets are not designed to address: they secure the signing process, not the decision-making process. They protect you from having your keys stolen — they do not protect you from making bad decisions about who to send your keys’ funds to.
In 2026, the crypto threat landscape has evolved significantly. According to Immunefi’s Web3 security report, the majority of crypto losses now come not from technical exploits but from social engineering, fraud, and exit scams — all of which target users who have hardware wallets but lack counterparty verification tools. And as noted in Elliptic’s DeFi risk research, sophisticated fraud operations specifically build clean-looking on-chain histories to pass surface-level checks — making behavioral AI analysis essential for detection.
The good news: the tools to verify counterparties now exist, are free, and take seconds to use. Here is what the complete security stack looks like beyond the hardware wallet.
ChainAware Fraud Detector: Verify Before You Pay
The ChainAware Fraud Detector answers the most fundamental counterparty question: is this wallet address trustworthy? It analyzes the behavioral patterns of any wallet address using predictive AI — achieving 98% accuracy in predicting whether an address is likely to commit fraud.
Critically, it is a predictive tool, not a forensic one. It does not just check whether an address has already been flagged — it analyzes behavioral interaction patterns to identify fraud risk before it materializes. This matters because sophisticated fraud operators specifically build clean-looking histories to avoid forensic detection. The Fraud Detector catches the behavioral signatures that databases miss.
The practical workflow is simple: before sending any meaningful amount of crypto to an unfamiliar address — a service provider, a P2P trade counterparty, a business contact — run the address through the Fraud Detector. A high Trust Score (above 0.70) is a green light. A low Trust Score is a reason to investigate further before signing anything with your hardware wallet.
For the complete guide to how the Fraud Detector works, see our Fraud Detector complete guide. For a full explanation of why Trust Scores are the essential complement to hardware wallet security, see our guide to Crypto Trust Score metrics.
ChainAware Rug Pull Detector: Check Pools Before You Invest
Hardware wallets are popular among DeFi users precisely because DeFi requires frequent transaction signing. But every DeFi interaction carries counterparty risk beyond smart contract security: the risk that the pool you’re providing liquidity to will rug pull, draining your position in a single transaction.
The ChainAware Rug Pull Detector predicts rug pull risk by analyzing the Trust Scores of the contract creator and liquidity providers — not by reading source code, which can be obfuscated or unavailable. Its core logic: a good pool is created by trusted actors. A rug pull will almost always involve either a new/low-trust creator, new/low-trust LPs, or both.
As documented in our Rug Pull Detector guide, approximately 95% of PancakeSwap pools end in rug pulls. Running the pool contract through the Rug Pull Detector before adding liquidity is one of the highest-value security checks available to DeFi users — free, instant, and requiring no technical expertise.
ChainAware Token Rank: Genuine Communities vs Fake Holders
One of the most sophisticated fraud vectors in 2026 is the manufactured token community. Projects inflate their holder counts with bot wallets, farming addresses, and coordinated airdrop recipients — creating the appearance of organic adoption that doesn’t exist. You buy in based on the community size. The community was always fake. The token dumps.
The ChainAware Token Rank cuts through this manipulation by measuring what holder counts cannot: the quality of token holders. Token Rank is calculated from the median Wallet Rank of all token holders — combining their experience levels, activity, protocol diversity, and trust scores into a single quality metric.
A token whose holders have high median Wallet Ranks is a token held by genuine, experienced Web3 participants. A token whose holders have low median Wallet Ranks is a token dominated by freshly-created wallets, bots, and farming addresses — regardless of what the headline holder count says. For the complete explanation, see our Token Rank complete guide.
ChainAware Wallet Auditor: Full Counterparty Intelligence
For deeper due diligence — on business partners, large P2P trades, KOL partnerships, or any high-value interaction — the ChainAware Wallet Auditor provides the complete behavioral profile of any wallet address: Experience Level, Risk Willingness, Predicted Intentions, Wallet Rank, AML Status, and Trust Score in a single view.
The Wallet Auditor is particularly useful for scenarios that the Fraud Detector’s single Trust Score doesn’t fully cover. Vetting a KOL before a partnership? Check whether their wallet history actually reflects the DeFi expertise they claim. Screening airdrop submissions? Filter genuine users from farming bots by Experience Level and Wallet Rank. Evaluating a new business partner’s treasury address? The full behavioral profile tells you far more than a name and a website. Full details in our Wallet Auditor guide.
Know Who You’re Dealing With
Wallet Auditor: Full Behavioral Profile of Any Address
Experience, Risk Willingness, Intentions, Wallet Rank, AML Status, Trust Score — the complete picture for any wallet on 8 networks. Essential for KOL vetting, airdrop screening, and high-value counterparty due diligence. Free.
Other Fraud Detection Tools Worth Using
ChainAware provides the most comprehensive behavioral intelligence stack, but a complete security setup benefits from multiple complementary tools:
Etherscan / BscScan / Solscan (block explorers). The foundational transparency tools for any blockchain. Before interacting with any contract or address, check it on the relevant block explorer — verified source code, transaction history, token holder lists, and contract creator information are all publicly available. A contract without verified source code is an immediate red flag for any significant interaction.
De.Fi Shield (formerly DeFi Safety). A risk scoring platform that rates DeFi protocols on security practices, smart contract quality, team transparency, and operational history. Useful for protocol-level due diligence before committing significant liquidity to a new platform.
Revoke.cash. A free tool that shows you all the token approvals your wallet has granted to smart contracts — and lets you revoke them. Unlimited token approvals granted to compromised or malicious contracts are a common source of fund loss. Regular approval audits with Revoke.cash are essential hygiene for active DeFi users.
Web3 Antivirus / Pocket Universe / Fire. Browser extensions that simulate transactions before you sign them — showing you exactly what will happen (what will leave your wallet, what will enter) before you approve anything with your hardware wallet. These tools catch a broad class of malicious transaction signatures that might otherwise slip past review.
Chainalysis Reactor / TRM Labs (institutional). For institutional users and crypto businesses, professional AML and transaction tracing platforms provide deep forensic analysis of fund flows. These complement ChainAware’s predictive behavioral analysis with historical forensic tracing — the two approaches together provide the most complete risk picture available.
The Complete 2026 Crypto Security Stack
A complete crypto security posture in 2026 looks like this — organized by what each layer protects:
Layer 1 — Private Key Protection: Hardware wallet (Ledger, Trezor, Coldcard, Keystone, or Passport depending on your use case). This layer ensures your private keys are never exposed to internet-connected environments and that you physically verify every transaction you sign.
Layer 2 — Counterparty Verification: Fraud Detector for payment counterparties, Rug Pull Detector for DeFi pools and contracts, Token Rank for token investment decisions, Wallet Auditor for deep due diligence. This layer ensures that the transactions you sign with your hardware wallet are going to trustworthy destinations.
Layer 3 — Transaction Hygiene: Regular approval revocation (Revoke.cash), transaction simulation (Web3 Antivirus / Pocket Universe), and block explorer verification before interacting with new contracts. This layer catches the specific vectors — malicious approvals, deceptive transaction simulations — that slip between Layers 1 and 2.
Layer 4 — Platform Monitoring (for Dapp teams): ChainAware Transaction Monitoring for continuous 24×7 screening of every wallet connecting to your platform. This layer protects your users and your platform from fraud at the infrastructure level — not just individual transaction level.
The total time investment for Layers 1-3 on any individual transaction: under 2 minutes. The potential loss prevented: your entire portfolio. The math is not subtle.
ChainAware.ai — Complete Counterparty Verification
Protect Your Keys. Verify Your Counterparties. Complete the Stack.
Fraud Detector for wallet addresses. Rug Pull Detector for pools. Token Rank for token quality. Wallet Auditor for full profiles. All free. All real-time. The security layer your hardware wallet can’t provide.
Frequently Asked Questions
Which hardware wallet is best for beginners in 2026?
The Trezor Safe 3 or Ledger Nano S Plus are the best starting points for beginners — both offer genuine Secure Element security at accessible price points (~$79) with user-friendly setup processes. The Trezor Safe 3 has the advantage of fully open-source firmware for users who appreciate community-audited security.
Is Ledger or Trezor safer?
Both are highly secure. The key architectural difference: Ledger uses a Secure Element chip with proprietary firmware; Trezor uses open-source firmware (Model T) or open-source firmware with Secure Element (Safe 3). Ledger’s closed-source firmware has faced criticism for its opacity; Trezor’s open-source approach has faced scrutiny after a 2023 security research report identified a potential seed phrase extraction vulnerability requiring physical access. For the vast majority of users, both represent excellent protection against the realistic threats they face — remote key theft being far more likely than physical device compromise.
Can my hardware wallet protect me from DeFi rug pulls?
No. Your hardware wallet will faithfully sign a transaction adding liquidity to a rug pull pool. The hardware wallet secures the signing process — it does not evaluate the destination. Use the ChainAware Rug Pull Detector to check pools before adding liquidity. It predicts rug pull risk by analyzing the Trust Scores of the contract creator and LPs — free and takes seconds.
What is the most important thing to protect about my hardware wallet?
Your 12 or 24-word seed phrase. This is the one item that, if compromised, renders the hardware wallet irrelevant — anyone with your seed phrase can reconstruct your wallet on any device without needing the physical hardware wallet. Store it in multiple secure offline locations, never photograph it, never type it into any computer or phone, and never share it with anyone — including anyone claiming to be from Ledger or Trezor support.
Do I need a hardware wallet if I only use major exchanges like Coinbase or Binance?
Exchange custody means the exchange controls your private keys — not you. Exchange hacks, insolvencies (as seen with FTX), and regulatory actions can all result in loss of access to exchange-held funds. For any amount you cannot afford to lose, self-custody via hardware wallet is strongly recommended. The crypto adage applies: not your keys, not your coins.
How do I verify a token has genuine holders before investing?
Use ChainAware Token Rank — it measures the median Wallet Rank of all token holders, revealing whether the holder base consists of genuine Web3 participants or low-quality bot/farming wallets. A high Token Rank indicates real community; a low rank signals artificial inflation regardless of what the headline holder count says.